Cyber Attack Campaign Targeting the Cuban Embassy and Global Government Entities
By Threat Intelligence Unit
Overview
Oasis Security identified a large-scale intrusion campaign targeting diplomatic infrastructure, government-affiliated entities, and strategic sector organizations across multiple regions.
The analysis is based on files and logs obtained from an attacker-controlled server, revealing coordinated activity involving email server exploitation, credential harvesting, vulnerability scanning, and large-scale reconnaissance operations.
The findings indicate that the activity extended beyond simple scanning and included confirmed compromise and data exfiltration.
Executive Summary
- Targeting of diplomatic and government-affiliated infrastructure
- Confirmed targeting of the Exchange email infrastructure associated with the Cuban Embassy
- Exploitation of Exchange SSRF vulnerability using publicly available code
- Automated credential harvesting using juicy365.py
- Large-scale scanning exploiting React vulnerability (CVE-2025-55182)
- Extensive IP and domain reconnaissance using kscan
- Confirmed data exfiltration including emails, credentials, documents, and identity-related information
Adversary Infrastructure Overview
Analyzed Server Information
- Server IP:
198.98.56.220 - Country: United States
Server-side files and logs were collected from an attacker-controlled system, providing insight into attacker tooling, operational workflow, and target scope.
Targeting of the Embassy of Cuba Email Infrastructure
Exchange SSRF Exploitation
The Exchange_SSRF directory contains the exchange_ssrf_attacks.py script.
- The script is designed to exploit vulnerabilities in Microsoft Exchange email servers
Identified Target Email Server Domains
[REDACTED]cuba.cu- associated with a Cuban embassy and its consular operations
Email Domain Configuration
[REDACTED]cuba.cu— identified as the Exchange server supporting a Cuban embassy email infrastructure[REDACTED]cuba.us— observed as the email domain used by targeted user accounts- The
[REDACTED]cuba.usdomain does not resolve in public DNS, suggesting use for internal routing within the Exchange environment
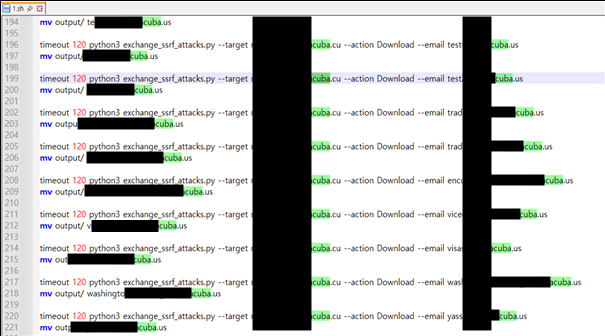
Figure 1. Log evidence showing targeted activity against a Cuba-related email server domain
Target List
- Approximately 88 subdirectories, each named in the format of an email address
- These are assessed to represent targeted user accounts
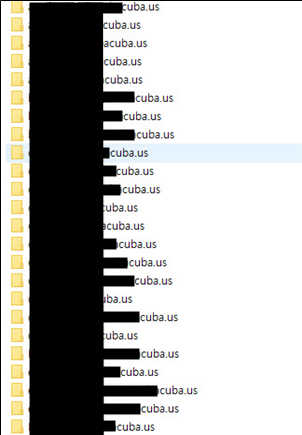
Figure 2. Directory structure mapping targeted email accounts
Data Exfiltration Evidence
Within the subdirectories:
.emlfiles containing full email contents- Documents and attachments
- Sensitive data including passport-related information

Figure 3. Sample of exfiltrated files including email data and documents
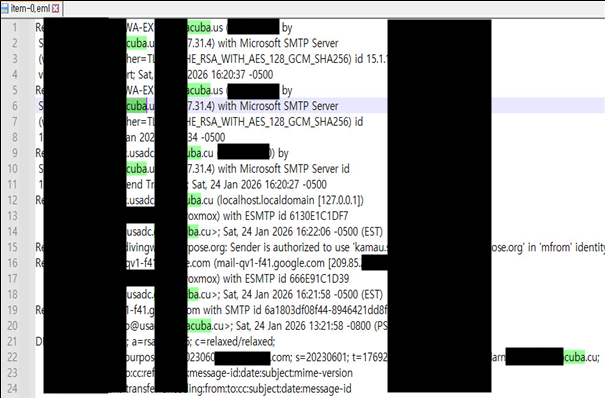
Figure 4. Extract from exfiltrated email data showing message metadata and headers
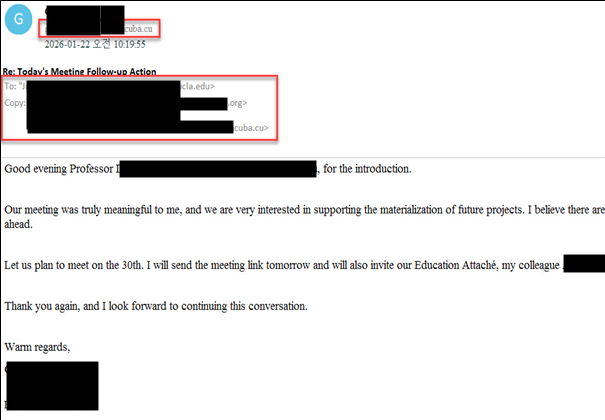
Figure 5. Sample of exfiltrated email communication from compromised accounts
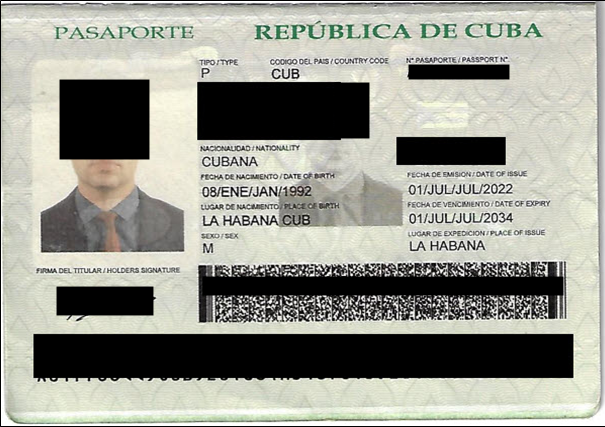
Figure 6. Sample of sensitive personal data identified within exfiltrated files
Analysis confirms that email addresses in the .eml files correspond to subdirectory names.
- Indicates account-level targeting and successful data extraction
Targeting of Government and Defense-Related Infrastructure
Data Exfiltration
The .bash_history file contains logs indicating targeting of government-affiliated and enterprise infrastructure.
Identified Target
- A subdomain associated with a government environmental regulatory organization in the United States
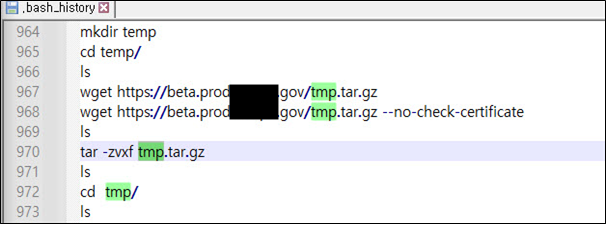
Figure 7. .bash_history file showing command execution targeting government-associated infrastructure
Exfiltrated Directory and File Structure
- Approximately 4,309 files and directories identified in
/tmp
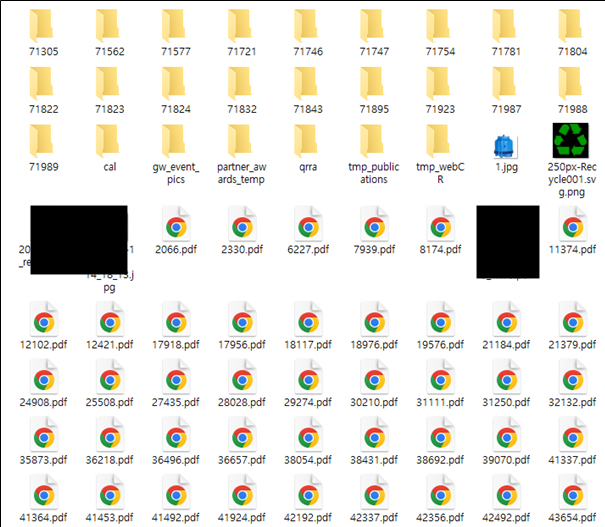
Figure 8. File structure identified in the /tmp directory containing large volumes of collected data
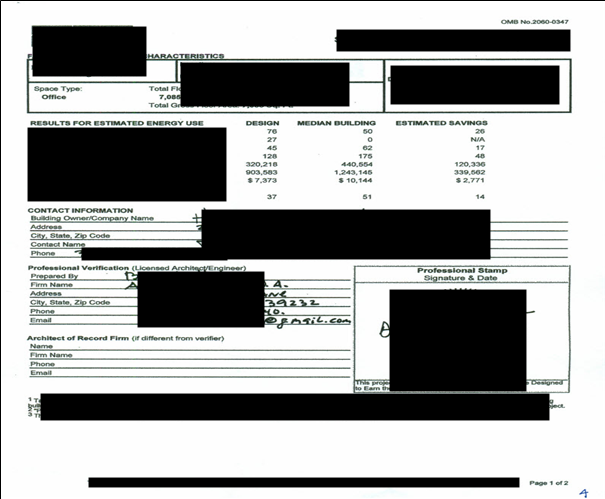
Figure 9. Sample of document file identified within the collected dataset (1)
Figure 10. Sample of document file identified within the collected dataset (2)
Credential Harvesting Activity
The logs confirm usage of juicy365.py which is a password validation tool.
- Carried out a credential harvesting attack targeting the U.S based defense-related company
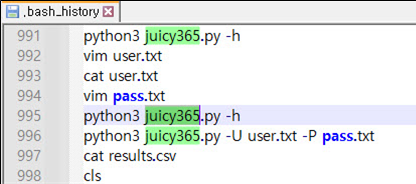
Figure 11. .bash_history file showing execution of the juicy365.py credential validation tool
Supporting Files
user.txt→ approximately 287 email addresses of the U.S based defense-related companyresults.csv→ email addresses, password attempts, and validation results
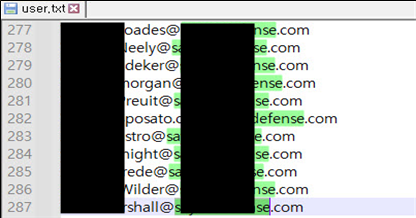
Figure 12. Sample of email addresses identified in the credential targeting list
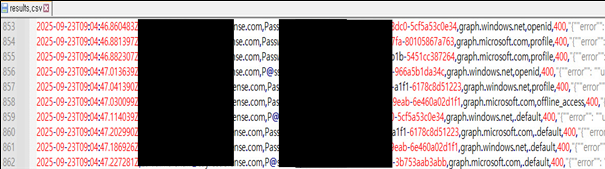
Figure 13. Results of credential validation attempts showing email-password combinations
This indicates targeting of defense-aligned service providers supporting government operations.
Targeting of Global Government and Strategic Entities
Identified Target Scope
Analysis revealed targeting across:
- Government financial authorities
- Foreign affairs-related institutions
- Maritime regulatory bodies
- State-linked energy organizations
- Financial institutions
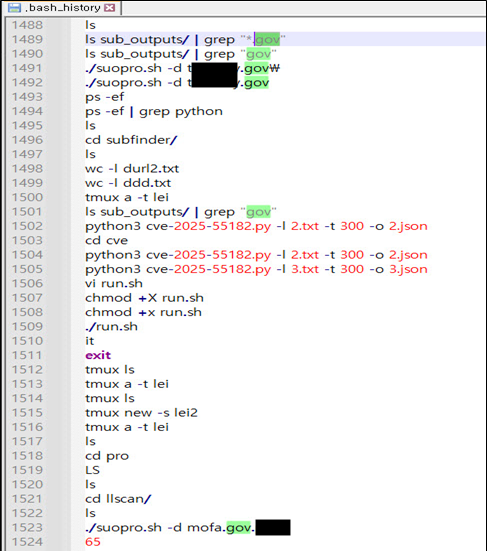
Figure 14. Scanning activity targeting government-associated domain
Observed Activity
- Data collection activity conducted using the
suopro.shscript - Multi-sector targeting observed across government, defense, energy, and financial sectors
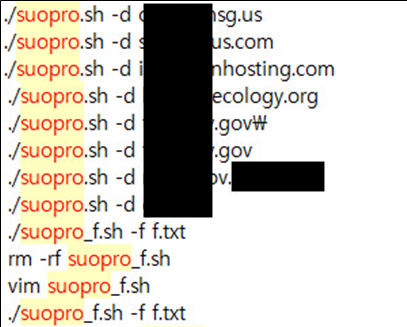
Figure 15. Data collection using suopro.sh
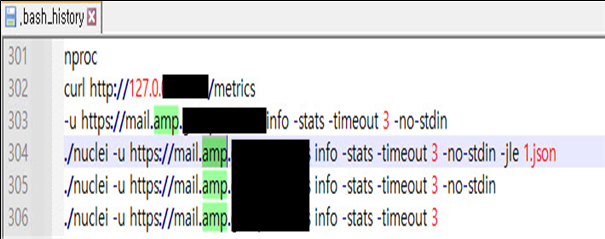
Figure 16. Evidence of scanning targeting government-associated infrastructure
Exploitation of React Vulnerability (CVE-2025-55182)
Scanning Activity
The .bash_history file confirms:
- Automated scanning exploiting CVE-2025-55182
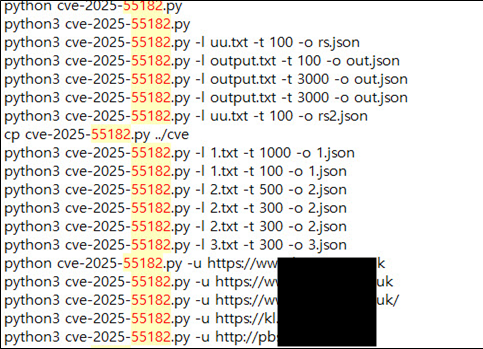
Figure 17. Evidence of automated scanning exploiting CVE-2025-55182
Identified Files
- 130 text files containing vulnerability scan results
- All indicate the presence of vulnerable systems
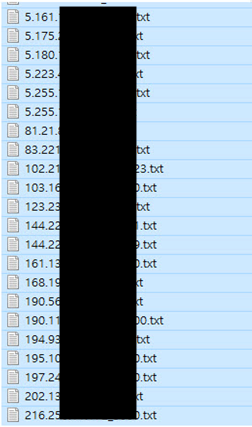
Figure 18. List of text files containing vulnerability scan results from automated scanning activity
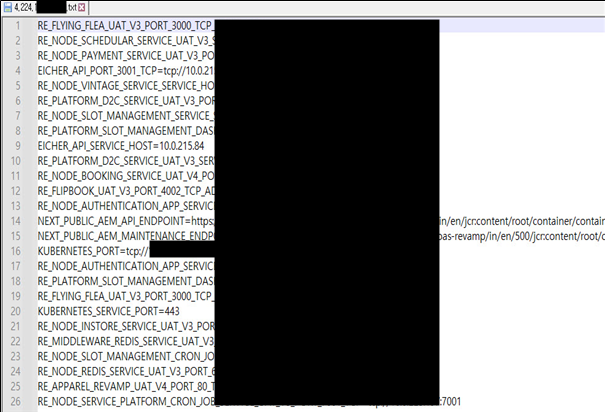
Figure 19. Extracted service and configuration details from vulnerable target systems
Additional Findings
- 5,252 text files identified in the
envcdirectory - Files contain server configuration data and extracted information from vulnerable systems
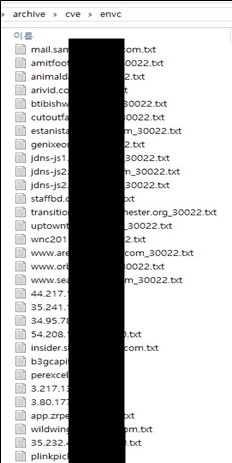
Figure 20. Directory listing of collected files containing extracted data from vulnerable systems
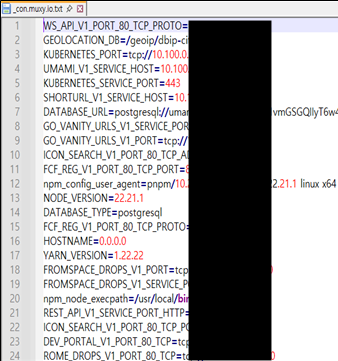
Figure 21. Sample of configuration data identified within collected files
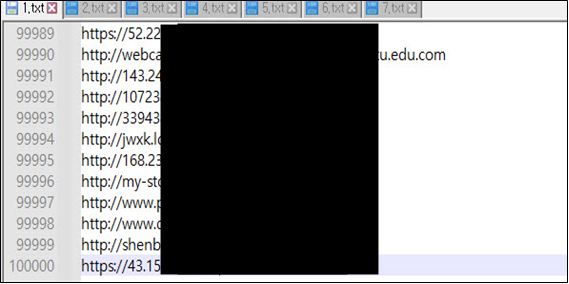
Figure 22. Sample of URLs and endpoints identified from large-scale data collection
Confirmed Compromise Case
Upon reviewing a text file associated with a successfully compromised regional IP:
- Server configuration details were exposed
- Indicates successful exploitation and data retrieval
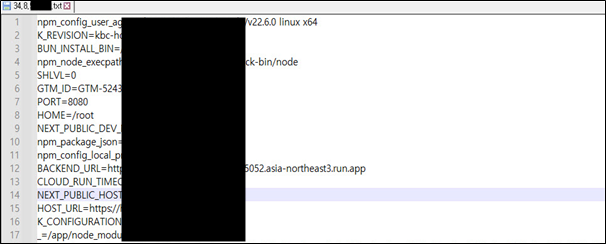
Figure 23. Extracted configuration data from a successfully compromised system
Large-Scale IP and Domain Scanning Activity
kscan Usage
The attacker conducted large-scale scanning using the kscan tool.
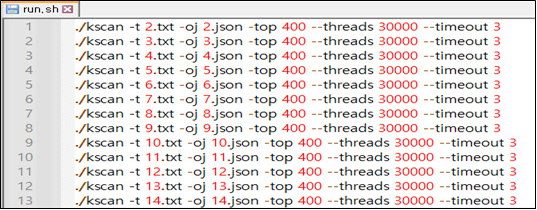
Figure 24. Evidence of large-scale IP and domain scanning using kscan
Observed Indicators
- Region-based scanning patterns identified
- Targeting of government-related domains within specific geographic clusters
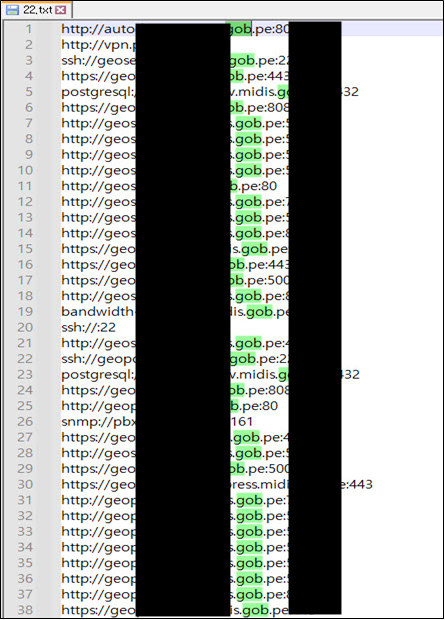
Figure 25. Sample of reconnaissance data targeting government-related domains
Target Domains
durl2.txtcontains approximately 11,235,470 domains
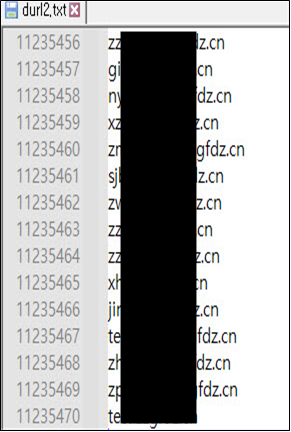
Figure 26. Large-scale domain dataset identified in durl2.txt
Conclusion
The analysis indicates that the attacker-controlled server was used for broad, multi-target intrusion operations, rather than a single isolated campaign.
The observed activity includes exploitation of Exchange SSRF vulnerabilities, automated credential harvesting, and large-scale vulnerability scanning targeting React-based systems, supported by extensive reconnaissance across a global domain space.
The presence of .eml files, credentials, and sensitive data suggests that multiple intrusions progressed beyond initial access and resulted in confirmed data exfiltration.
In addition, the collection of thousands of vulnerable server configuration files across a wide geographic range highlights the use of a highly automated and scalable attack infrastructure, reinforcing the assessment that this activity represents a coordinated campaign.
Overall, the activity is assessed as an intelligence-gathering intrusion campaign targeting diplomatic infrastructure and strategic sectors, with potential implications extending beyond financially motivated cybercrime.