Analysis of Attacks Targeting Israel and Global Government Entities via CVE-2025-55182 Exploitation
By Threat Intelligence Unit
Overview
Oasis Security identified a large-scale automated scanning and exploitation campaign targeting government infrastructure worldwide. The activity demonstrated a heavy concentration on Israel-associated networks, with spillover targeting observed across the United States, Europe, Africa, and Asia.
Analysis of attacker-controlled infrastructure indicates active exploitation attempts leveraging recently disclosed React framework vulnerabilities, rather than passive reconnaissance. Collected artifacts further suggest attacker-side aggregation and validation of vulnerable assets in preparation for follow-on activity.
Executive Summary
- Large-scale automated scanning campaign targeting global government infrastructure
- Heavy focus on Israeli networks with secondary targeting across multiple regions
- Active exploitation attempts using recently disclosed React vulnerabilities
- Evidence of attacker-side data aggregation and validation workflows
Adversary Infrastructure Overview
Analyzed Server Information
- C2 IP:
141.11.187.165 - Country: Netherlands
Collected Artifacts
A significant number of server-side artifacts were obtained from the analyzed C2 server, including:
- Target lists containing domains and IP addresses
- Python scripts for ASN-based network enumeration
- Automated scanning tools designed to exploit React vulnerabilities
- Scan output files containing confirmed vulnerable systems
Attack Tools and Capabilities
Analysis indicates the use of Python-based tooling to perform ASN-level reconnaissance and vulnerability validation targeting Israel-associated networks.
The tooling specifically focused on identifying systems vulnerable to the following React framework vulnerabilities:
- CVE-2025-55182
- CVE-2025-66478
Shodan was leveraged to identify candidate IP addresses potentially affected by these vulnerabilities prior to direct scanning.
Python-Based Reconnaissance and Scanning Scripts
- t.py: Used to enumerate IP address ranges associated with Israel-related ASNs and store results for follow-on scanning.
- i.py: Performed similar ASN-based network discovery; multiple in-code comments were written in Persian.
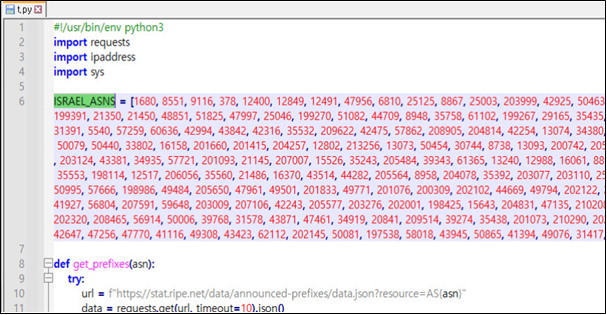
Figure 1. Python script used to collect and aggregate IP address ranges associated with Israel-related ASNs
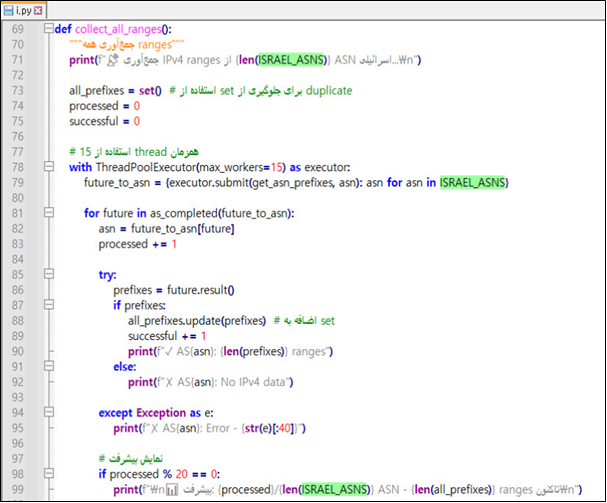
Figure 2. Python reconnaissance script performing ASN-based IP enumeration with Persian-language code comments
Target Intelligence and Reconnaissance Data
Collected datasets indicate large-scale targeting of Israel-associated infrastructure and government-operated systems across multiple countries.
Israel-Associated Infrastructure
- 88,220 IP addresses and ports associated with Israeli networks (
88220-il.txt) - Subdomain enumeration for Israeli academic domains, including
wincol.ac.il(wincolsub.txt)
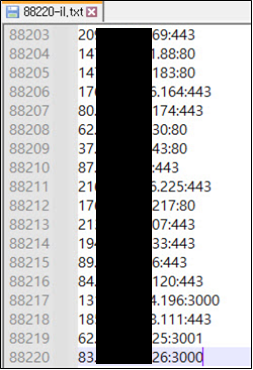
Figure 3. IP address and port combinations enumerated from Israel-associated ASN ranges
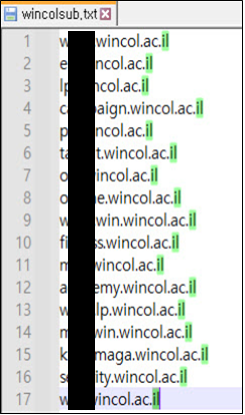
Figure 4. Subdomain enumeration results for Israel-based academic domain wincol.ac.il
Government Infrastructure Across Multiple Countries
- 1,538 government IP addresses identified globally (
1500-gov.txt) - 974 domains identified as potential targets (
target.txt) - Identified targets span multiple countries, including United States, Rwanda, India, and Colombia
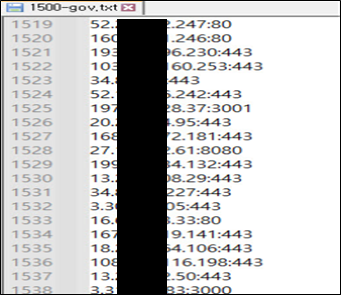
Figure 5. Government IP address list collected as scanning targets prior to vulnerability validation
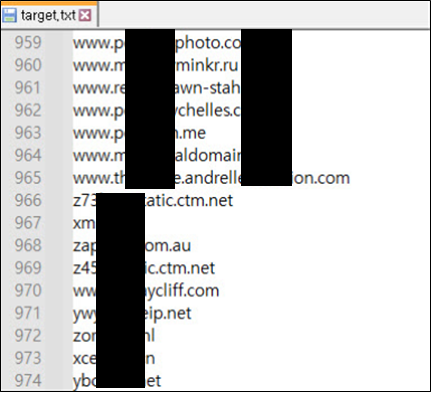
Figure 6. Aggregated domain list compiled as potential targets for vulnerability scanning
Exploitation Logs and Vulnerable Assets
Analysis of scan output files revealed numerous systems confirmed as vulnerable to the exploited React framework vulnerabilities.
Confirmed Vulnerable Systems
| Dataset | Affected IPs | Coverage / Breakdown |
|---|---|---|
out-1500-gov.txt | 43 | United States (18), Rwanda (4), India (4), Colombia (2) |
out-gov.txt | 9 | United States (1), Rwanda (1), Nigeria (1), Malaysia (1), Cambodia (1) |
out-us.txt | 754 | United States |
out-88.txt | 10 | Israel (5), Germany (2), etc. |
out-16860.txt | 4 | US (3), Russia (1) |
out-88220.txt | 3 | Israel, US, Netherlands |
new.result | 26 | Israel (10), US (8), etc. |
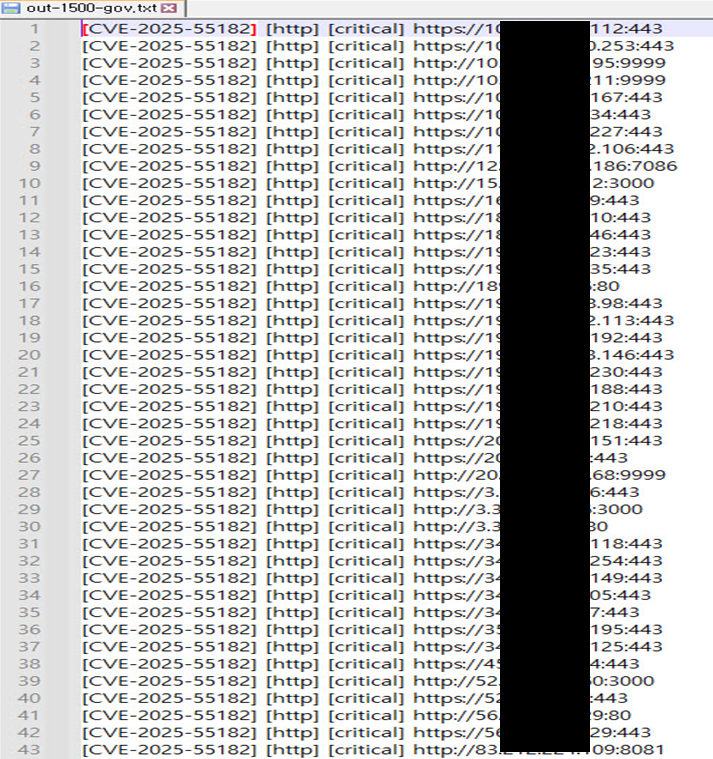
Figure 7. Scan output confirming multiple government-operated systems vulnerable to CVE-2025-55182
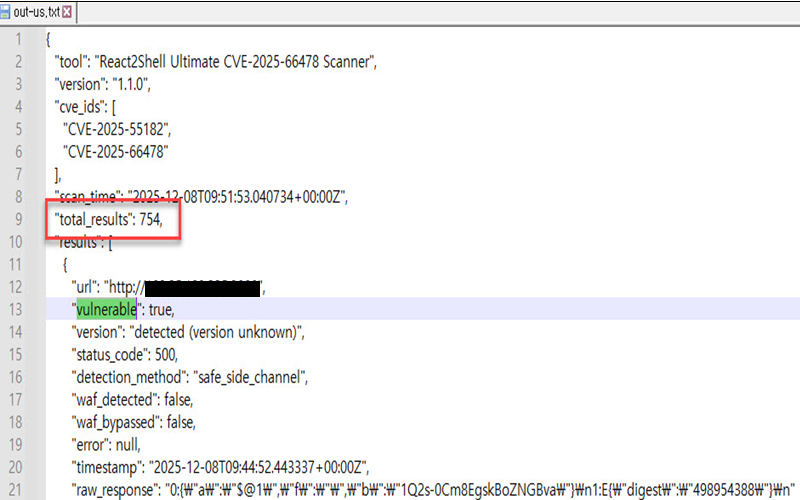
Figure 8. Automated scan results confirming 754 vulnerable systems identified across United States infrastructure
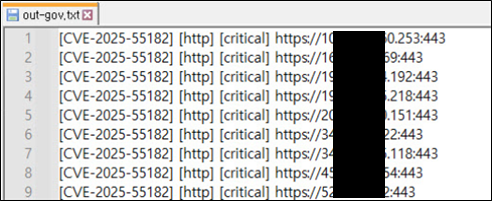
Figure 9. Scan output file listing government-operated systems identified as vulnerable to CVE-2025-55182
Threat Actor Attribution Signals
Linguistic Indicators
- Persian-language comments were identified within multiple reconnaissance scripts.
Geopolitical Targeting Indicators
- Repeated and concentrated scanning of Israel-associated network ranges
- Consistent prioritization of Israeli and government-operated infrastructure
Conclusion and Recommendations
Following the public disclosure of high-impact vulnerabilities, it is a well-established pattern that multiple threat actors rapidly conduct large-scale scanning and exploitation attempts to secure initial access to exposed systems. These activities are typically opportunistic in nature, with attackers prioritizing speed and coverage to obtain server-level control before defensive measures are broadly implemented.
Observed attacker infrastructure and activity in this case are consistent with early-phase exploitation behavior, including automated vulnerability validation and preparation for potential post-exploitation use. The identification of vulnerable government-linked IP addresses across more than 17 countries underscores the elevated risk posed by unpatched, internet-exposed assets during the immediate post-disclosure window.
Organizations are strongly advised to:
- Immediately apply security patches addressing CVE-2025-55182 and CVE-2025-66478
- Update React framework deployments to the latest supported versions
- Enforce network-level controls to limit access from infrastructure associated with observed scanning and exploitation activity
- Enhance continuous attack surface and exposure monitoring