Multi-Stage Cyber Campaign Targeting Middle Eastern Critical Sectors with Tradecraft Consistent with MuddyWater
By Threat Intelligence Unit
Overview
Oasis Security analyzed a campaign in which the threat actor conducted broad reconnaissance across more than 12,000 internet-exposed systems by weaponizing at least five newly disclosed vulnerabilities. This large-scale scanning activity was followed by selective intrusion attempts targeting critical sectors in the Middle East, including aviation, energy, and government entities.
The operation leveraged a combination of vulnerability exploitation, Outlook Web Access (OWA) brute-force attacks, and newly identified Command and Control (C2) controllers supporting multi-protocol communication. The activity progressed beyond reconnaissance and access attempts, resulting in confirmed exfiltration of sensitive data from compromised environments.
The operation exhibits a structured multi-stage workflow, credential-focused intrusion, and novel C2 controllers that align with previously observed MuddyWater tradecraft.
Executive Summary
- The campaign followed a structured multi-stage workflow, transitioning from large-scale reconnaissance to selective intrusion and data exfiltration.
- The actor scanned more than 12,000 internet-exposed systems using at least five newly disclosed CVEs.
- The operation shifted from broad reconnaissance to targeted attacks against aviation, energy, and government sectors in the Middle East.
- Credential harvesting via OWA brute-force attacks served as a primary intrusion vector.
- Newly identified C2 controllers were observed, with communication patterns consistent with those previously associated with MuddyWater.
- Sensitive data, including passport, payroll, and financial records, was confirmed to be exfiltrated.
Adversary Infrastructure
- Server IP:
157.20.182.49 - Country: Netherlands
A large number of attacker-controlled server-side files were collected from this infrastructure, indicating coordinated activity spanning large-scale vulnerability scanning, credential harvesting, and data staging.
The artifacts also reveal the presence of modular C2 components and operational scripts, highlighting a multi-protocol communication design and organized controller structure used to manage compromised hosts.
Adversary C2 Controller
Analysis of attacker-controlled infrastructure revealed a modular and flexible Command and Control (C2) architecture composed of multiple controller implementations and communication channels.
Key characteristics include:
- Multi-language implementation: Python-based controllers (e.g.,
tcp_serv.py,udp_3.0.py) and Go-based binaries (server,client.exe) - Multi-protocol communication: TCP (port 5009), HTTP-based endpoints (e.g.,
/command,/result,/signup,/feed), and UDP-based channels - Encrypted communication: AES (CTR mode)-encrypted data exchange observed in HTTP-based controllers
- Session control mechanisms: Cookie-based client identification (e.g.,
cidvalues) used to manage infected hosts - Custom communication format: Header structures (e.g.,
<BIIH) consistently observed across multiple controllers
Multiple controller variants were identified across different directories, including lightweight Python-based listeners and more advanced HTTP-based controllers capable of handling encrypted client communication and tasking.
Notably, certain communication methods and operational patterns observed in these controllers closely align with techniques previously associated with the MuddyWater threat group, including the ArenaC2 framework.
The tcp_serv.py controller listens on port 5009 and accepts inbound connections from compromised systems, while udp_3.0.py operates as a UDP-based controller with similar communication structures. In parallel, HTTP-based controllers observed in other directories handle encrypted data exchange and client management through defined API-like endpoints.
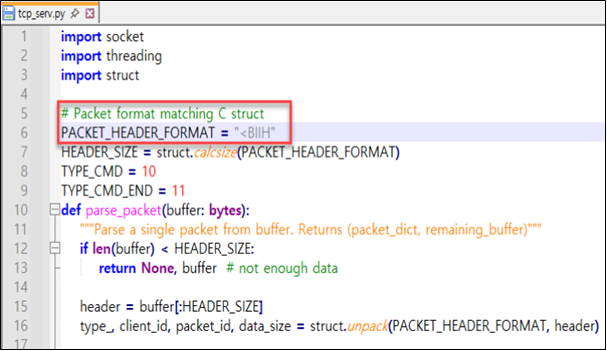
Figure 1. TCP-based C2 controller (tcp_serv.py) using a custom <BIIH header structure
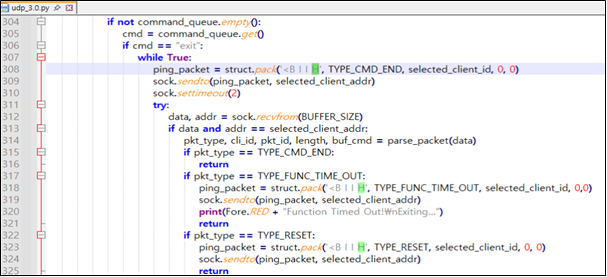
Figure 2. UDP-based C2 controller (udp_3.0.py) using a custom <BIIH header structure
The ex-server file identified as a Go-based malware controller communicates over HTTP and receives AES (CTR)-encrypted data via the /signup and /feed endpoints.
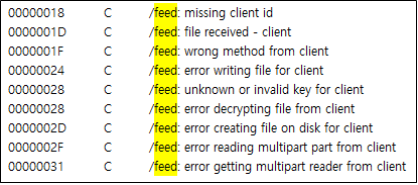
Figure 3. Logic associated with the /feed endpoint of ex-server
Campaign Analysis
The campaign follows a structured operational pipeline rather than isolated attack attempts.
The actor conducted large-scale scanning to identify vulnerable systems, followed by targeted credential harvesting activities. Successful access enabled data collection and staging, ultimately leading to exfiltration.
This workflow demonstrates a coordinated approach combining opportunistic discovery with selective exploitation.
Vulnerability Exploitation and Reconnaissance Strategy
The campaign demonstrated a coordinated approach combining large-scale reconnaissance with rapid weaponization of newly disclosed high-risk vulnerabilities.
The actor conducted extensive scanning across more than 12,000 internet-exposed systems by leveraging at least five distinct CVEs, targeting a wide range of platforms, including:
- Web applications
- Email servers
- IT management and monitoring systems
- Workflow and automation platforms
Rather than exploiting all identified targets, the operation followed a two-phase model: broad reconnaissance to identify vulnerable systems, followed by selective exploitation of high-value targets.
This transition from indiscriminate scanning to targeted intrusion reflects a structured and resource-efficient operational strategy.
The scale and organization of scanning activity—combined with vulnerability-specific target grouping—indicate an automated and continuously operating reconnaissance capability.
CVE-2025-54068 — Laravel Livewire RCE
Target Surface: Web applications (Laravel Livewire v3)
Figure 4. Evidence of large-scale reconnaissance targeting CVE-2025-54068
CVE-2025-52691 — SmarterMail RCE
Target Surface: Email server software (SmarterMail)
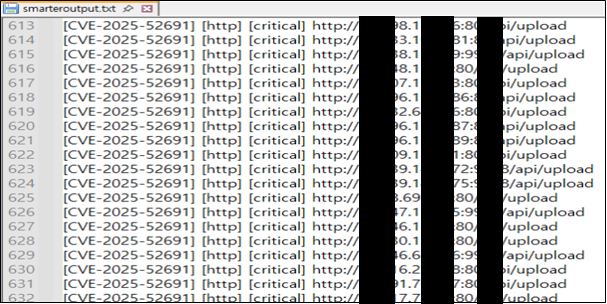
Figure 5. Evidence of large-scale reconnaissance targeting CVE-2025-52691
CVE-2025-68613 — n8n RCE
Target Surface: Workflow automation platform (n8n)
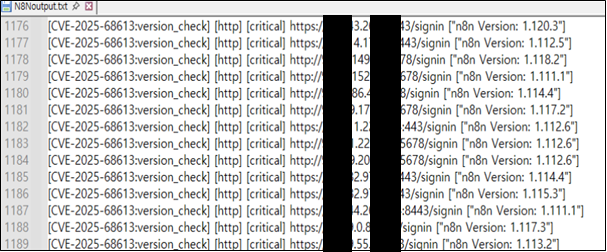
Figure 6. Evidence of large-scale reconnaissance targeting CVE-2025-68613
CVE-2025-9316 — Unauthenticated Session ID Generation
Target Surface: Remote monitoring and management (RMM) systems
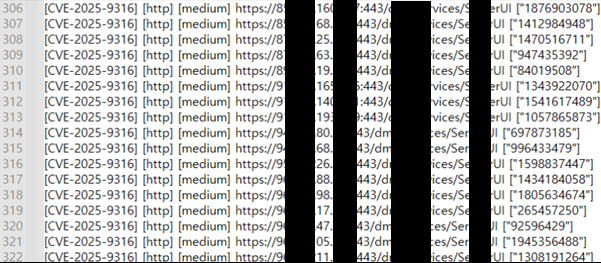
Figure 7. Evidence of large-scale reconnaissance targeting CVE-2025-9316
CVE-2025-34291 — Langflow RCE
Target Surface: AI workflow and automation platform (Langflow)
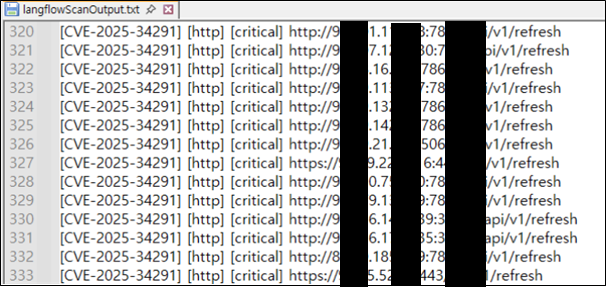
Figure 8. Evidence of large-scale reconnaissance targeting CVE-2025-34291
Credential Harvesting Operations
Credential-based intrusion played a central role in the campaign’s later stages, following large-scale vulnerability reconnaissance.
Observed techniques include:
- OWA brute-force attacks using custom scripts (
owa.py) - Multi-threaded credential attacks leveraging tools such as Patator
- Targeted username enumeration against specific organizations
These activities were directed at organizations in the Middle East, including entities in Egypt, Israel, and the United Arab Emirates. In several cases, user account lists and credential pairs were identified, indicating active attempts to gain access to enterprise email systems.
This reflects a transition from vulnerability-based discovery to credential abuse, increasing the likelihood of successful compromise even in partially secured environments.
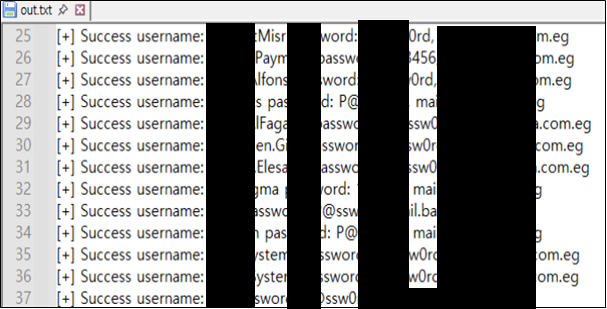
Figure 9. Evidence of successful credential harvesting via OWA brute-force attacks against an Egyptian firefighting enterprise
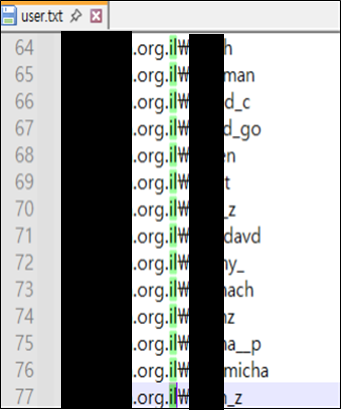
Figure 10. User account list associated with a targeted Israeli organization
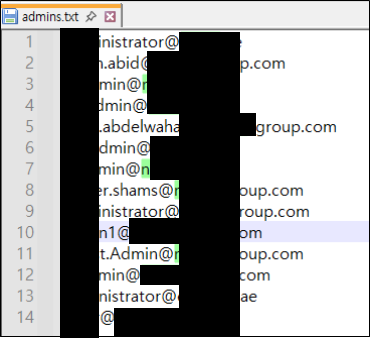
Figure 11. Administrator account list associated with a targeted organization in the United Arab Emirates
Data Exfiltration
The campaign progressed beyond initial access and resulted in confirmed data exfiltration from targeted environments.
Importantly, the exfiltrated data was associated with an aviation organization based in Egypt, indicating that the attack moved beyond reconnaissance and credential harvesting into successful compromise and data theft.
Exfiltrated data includes:
- Passport and visa records
- Payroll and salary information
- Credit card data
- Internal corporate documents
Approximately 200 files were identified within attacker-controlled directories, indicating structured data collection and staging prior to exfiltration.
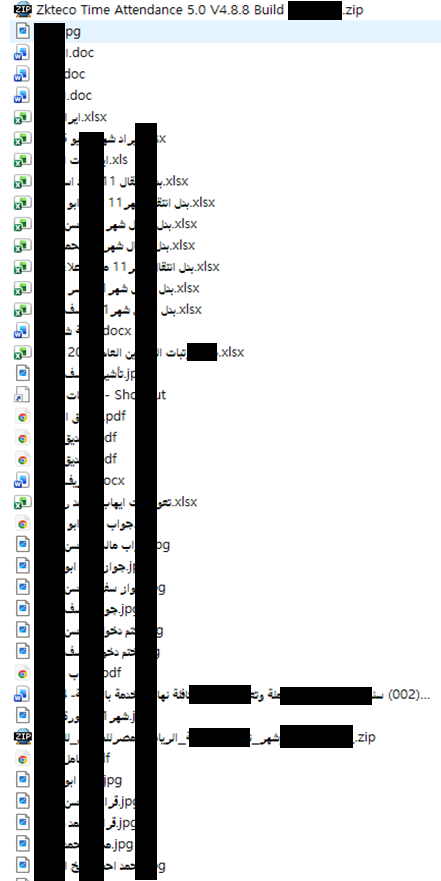
Figure 12. Evidence of staged data exfiltration from an Egyptian aviation organization
Key Targeted Sectors and Entities
The campaign demonstrates a clear transition from global reconnaissance to regionally focused targeting, with a particular emphasis on organizations in the Middle East.
Primary targets include:
- Aviation organizations
- Energy and infrastructure companies
- Public sector entities
Observed intrusion attempts and credential harvesting activities were concentrated on entities located in countries such as Egypt, the United Arab Emirates, and Israel.
The selection of sectors—particularly aviation and energy—indicates a focus on organizations with high operational and geopolitical relevance, where successful access could provide both intelligence value and potential disruption capabilities.
Additional targeting was also identified across entities in Portugal and India.
This pattern indicates deliberate target selection aligned with regional intelligence collection objectives, rather than opportunistic exploitation, and reflects a level of operational planning consistent with structured, campaign-driven activity.
Conclusion
This campaign demonstrates a structured attack lifecycle, progressing from large-scale reconnaissance to targeted intrusion and confirmed data exfiltration.
The actor combined vulnerability scanning across more than 12,000 systems, credential harvesting via OWA brute-force attacks, and modular multi-protocol C2 infrastructure to gain access to selected high-value targets. The confirmed exfiltration of sensitive data from an aviation organization in Egypt highlights that the operation moved beyond reconnaissance into successful compromise.
The observed shift from indiscriminate global scanning to regionally focused targeting—particularly in the Middle East—indicates a transition from opportunistic activity to selective, high-value targeting.
Notably, the activity was first identified in early February, immediately preceding the escalation of geopolitical tensions in the Middle East. The timing raises the possibility that the campaign was conducted in alignment with a broader strategic context.
In addition, the use of newly identified C2 controllers sharing characteristics with infrastructure attributed to MuddyWater further reinforces the assessment of a structured and coordinated campaign.
Overall, this campaign reflects a broader trend toward pipeline-driven cyber operations, where reconnaissance, credential abuse, and data exfiltration are tightly integrated into a single workflow.