Identification of Public IP Infrastructure Linked to Dark Web Illicit Services
By Threat Intelligence Unit
Executive Summary
- A dark web site supporting Bitcoin mixers and selling hacked cryptocurrency wallets was identified.
- The dark web site was confirmed to be hosted by a Tor hosting service.
Site Analysis
The identified site was a dark web–based service supporting Bitcoin mixers and illicit cryptocurrency-related services.
The site offered a range of illegal services, including:
- Bitcoin mixing services
- Sale of stolen cryptocurrency wallets
- Wallet hacking services
Access Information
- Onion Domain:
bitcoinpvcaacv6wgvwqpw35gufypz2ynbnak24vsoylghayrw7v5wid.onion
During the initial investigation, the onion domain was active and accessible. However, at the time of writing, the site is no longer reachable.

Figure 1. Bitcoin hacking and illicit cryptocurrency services interface
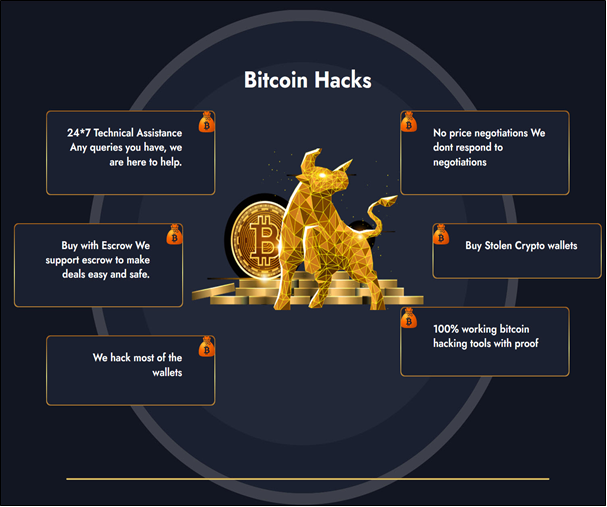
Figure 2. Content promoting Bitcoin hacking and illicit cryptocurrency services
Although the actual number of users could not be independently verified, the site advertised a high volume of users and completed orders, suggesting active operations at the time of observation.

Figure 3. Activity indicators advertised by the service
Infrastructure Analysis
Public IP Identification
The public IP address associated with the site was identified through Oasis Security’s dark web infrastructure analysis service Arthur.
- Public IP Address:
84.234.***.*** - Location: Romania
- Hosting Provider: THCPROJECTS
- ASN: AS51177
This indicated that the service relied on infrastructure that was partially exposed beyond the Tor network.
Additional Findings
- Google Analytics ID:
G-1ME4K0RD7K
Correlation analysis using the Google Analytics ID did not reveal any additional associated infrastructure or related entities.
- Onion Hosting Service
The server hosting environment was identified as Hide’n SeeK Tor Hosting.
Onion Domain: ydoc33j5oz3uythdwlm3a4euk3bnzpkudonqkppcd6kubs5fgie73tad.onion
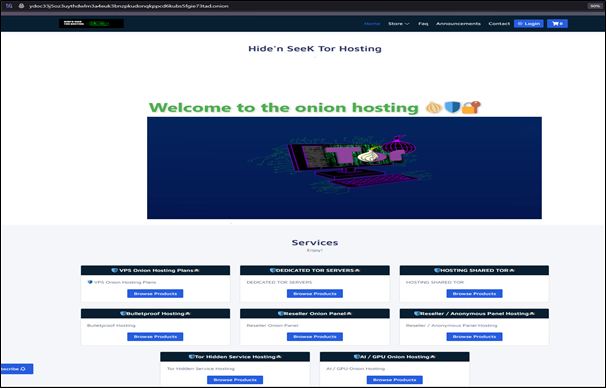
Figure 4. Hide’n SeeK Tor Hosting site interface
Conclusion
A dark web site offering Bitcoin mixing and wallet hacking services was identified, highlighting illicit cryptocurrency-related activities. The discovery of publicly exposed infrastructure suggests incomplete isolation from the Tor network and potential opportunities for further tracking and analysis.