SQL Injection and Reconnaissance Activity Targeting Hungarian ISP Systems and Commercial Web Services
By Threat Intelligence Unit
Overview
Oasis Security identified attacker-controlled infrastructure associated with SQL injection activity targeting multiple internet-facing systems, including ISP-related hostnames and commercial web services.
The observed activity includes successful database enumeration via automated tools, as well as broader reconnaissance targeting high-value domains.
Notably, the attacker leveraged both ghauri and sqlmap, indicating structured and repeatable exploitation attempts rather than opportunistic probing.
Adversary Infrastructure
- IP:
62.171.148.163 - Location: Germany
The infrastructure is actively used for:
- Web application exploitation
- Backend database enumeration
- Target reconnaissance
The combination of tooling and activity suggests deliberate and repeatable attack workflows, rather than opportunistic scanning.
Attack Activity
SQL Injection via Ghauri
The attacker conducted SQL injection activity using the ghauri tool against a hostname associated with a Hungarian telecommunications network.
The hostname (c-***.***.***.***.***.hu) appears to be linked to telecommunications infrastructure and is likely associated with a network interface, potentially corresponding to an aggregation-layer routing system within the ISP environment.
The observed activity indicates interaction with a backend database, resulting in enumeration of approximately 243 tables.
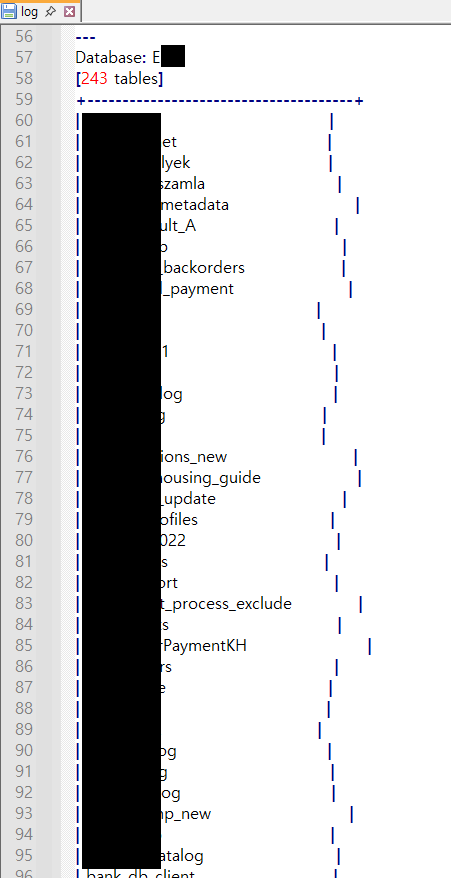
Figure 1. Database schema enumeration output showing 243 tables identified on the target system
This indicates successful interaction with a backend database, suggesting that the targeted system exposed a database-connected web interface, potentially intended for internal management or monitoring.
SQL Injection via SQLMap
In parallel, the attacker used sqlmap to target a separate web service:
- Target:
vi********.au - Sector: Smart home / AV installation services (Australia)
The activity resulted in:
- Successful database schema enumeration
- Discovery of approximately 77 tables
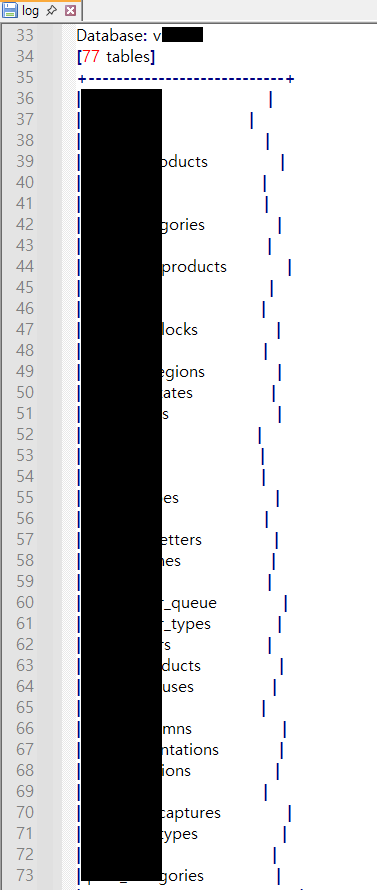
Figure 2. Database schema enumeration output showing 77 tables identified on the target system
This confirms that the attacker achieved visibility into backend database structures, which may enable further data extraction depending on access privileges.
Target Exposure Analysis
ISP-Associated Systems
One of the notable aspects of this activity is the targeting of a hostname associated with telecommunications infrastructure.
While the hostname appears to resolve to a system linked to router or interface management, the observed SQL injection behavior suggests:
- Presence of a web-accessible interface
- Backend database connectivity exposed through that interface
This suggests indirect exposure of internal infrastructure components via web services, rather than direct compromise of networking equipment.
Commercial Web Service Targeting
The second confirmed target is a public-facing commercial website operating in the smart home and AV installation sector.
The successful SQL injection suggests insufficient defensive controls such as:
- lack of input validation
- absence of parameterized queries
- inadequate web application firewall (WAF) protections
Additional Reconnaissance Activity
The attacker infrastructure contained multiple text files storing large volumes of subdomain data associated with U.S. military (.mil) domains.
The datasets appear to consist of aggregated subdomain listings, likely collected to support mapping of externally exposed services and potential entry points across military domain space.
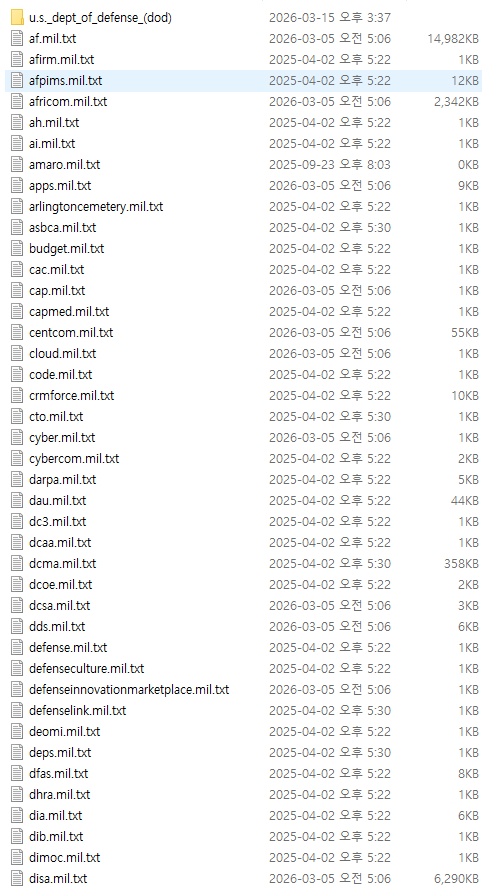
Figure 3. Subdomain enumeration datasets associated with U.S. military (.mil) domains
No direct evidence of exploitation or follow-on activity targeting these domains was identified in the available artifacts.
However, the presence of curated subdomain datasets strongly indicates:
- pre-attack reconnaissance activity
- potential preparation for future exploitation campaigns
Assessment
The observed activity demonstrates a multi-target SQL injection campaign with the following characteristics:
- Use of automated exploitation tools (ghauri, sqlmap)
- Focus on database enumeration as an initial objective
The inclusion of defense-related subdomain datasets suggests possible expansion of targeting scope or staging for follow-on operations.
Conclusion
This activity highlights the continued effectiveness of SQL injection as an initial access and reconnaissance technique, particularly in environments where management interfaces are misconfigured, legacy web applications remain in use, or backend services are insufficiently protected.
Organizations should maintain strict input validation practices, implement parameterized queries, enforce proper access controls for management interfaces, and continuously monitor for patterns indicative of automated exploitation activity.
Even limited database enumeration, such as table discovery, can provide attackers with critical insight into system structure, enabling more targeted and significant follow-on attacks.