Data Breach Affecting Egyptian Professional Syndicate Platform
By Threat Intelligence Unit
Overview
Oasis Security identified attacker-controlled infrastructure associated with a compromise affecting an Egyptian digital services platform used by professional syndicates and labor unions.
Attacker-side artifacts indicate that approximately 9,000 user profiles, including personal information and photographs, were successfully exfiltrated.
Because the platform primarily serves highly trusted professional groups such as engineers, doctors, and nurses, the breach introduces significant downstream risks including targeted fraud, identity abuse, and financial exploitation.
Adversary Infrastructure
- IP:
94.250.201.212 - Location: Germany
The identified infrastructure appears to have been used to manage the compromise and collect stolen information.
While additional attack attempts were observed targeting organizations across the Middle East, North Africa, Europe, and Asia, available artifacts only confirm successful data extraction from the Egyptian professional services platform.
Attacker Tooling Observed
Analysis of the attacker infrastructure revealed a Python-based data enumeration script used to automate large-scale collection of user information from the affected platform.
The script iterates through a predefined range of sequential user identifiers, issuing authenticated requests to internal API endpoints in order to retrieve user records.
Key characteristics of the script include:
- Enumeration of user IDs within a defined numeric range
- Use of authenticated session cookies to access backend APIs
- Automated retrieval of user profile information
- Controlled request timing to avoid triggering rate-limiting defenses
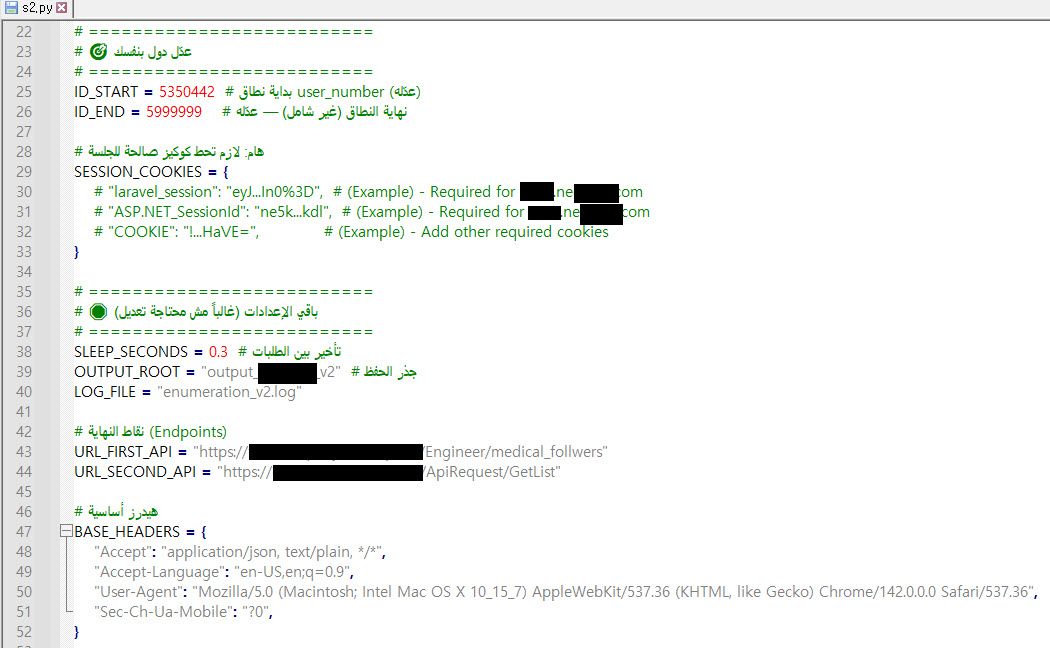
Figure 1. Python-based enumeration script used to automate API queries
This tooling strongly indicates that the compromise involved deliberate and automated data harvesting, rather than opportunistic or manual access.
Several code comments in the script are written in Arabic, providing a linguistic artifact that may offer contextual insight into the tool's development.
Compromised Platform
Egyptian Professional Syndicate Services Platform
- Domain: ne******.com
- Sector: Professional Services / Fintech Platform
The affected platform provides digital services for members of professional unions and syndicates, enabling online management of administrative processes and benefits through both web and mobile applications.
Key services supported by the platform include various administrative and benefit-related services for members of professional organizations.
Because the platform aggregates identity, financial, and medical-related information for large professional communities, it represents a high-value target for attackers.
Exposed Data
Evidence obtained from the attacker infrastructure indicates that approximately 9,000 user records were successfully exfiltrated from the affected platform.
The stolen dataset contains personally identifiable information such as names, date of birth, gender, address information, and numeric identity identifiers, along with additional internal platform identifiers.
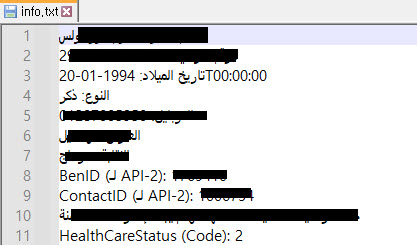
Figure 2. Sample of stolen user records recovered from attacker infrastructure
The user records show structured user profile data retrieved from backend platform APIs.
In addition to identity-related information, the dataset also includes internal identifiers such as BenID and ContactID, as well as healthcare-related status codes.
Notably, the attacker also collected user profile photographs, further increasing the risk of identity abuse, impersonation, and targeted social engineering attacks.
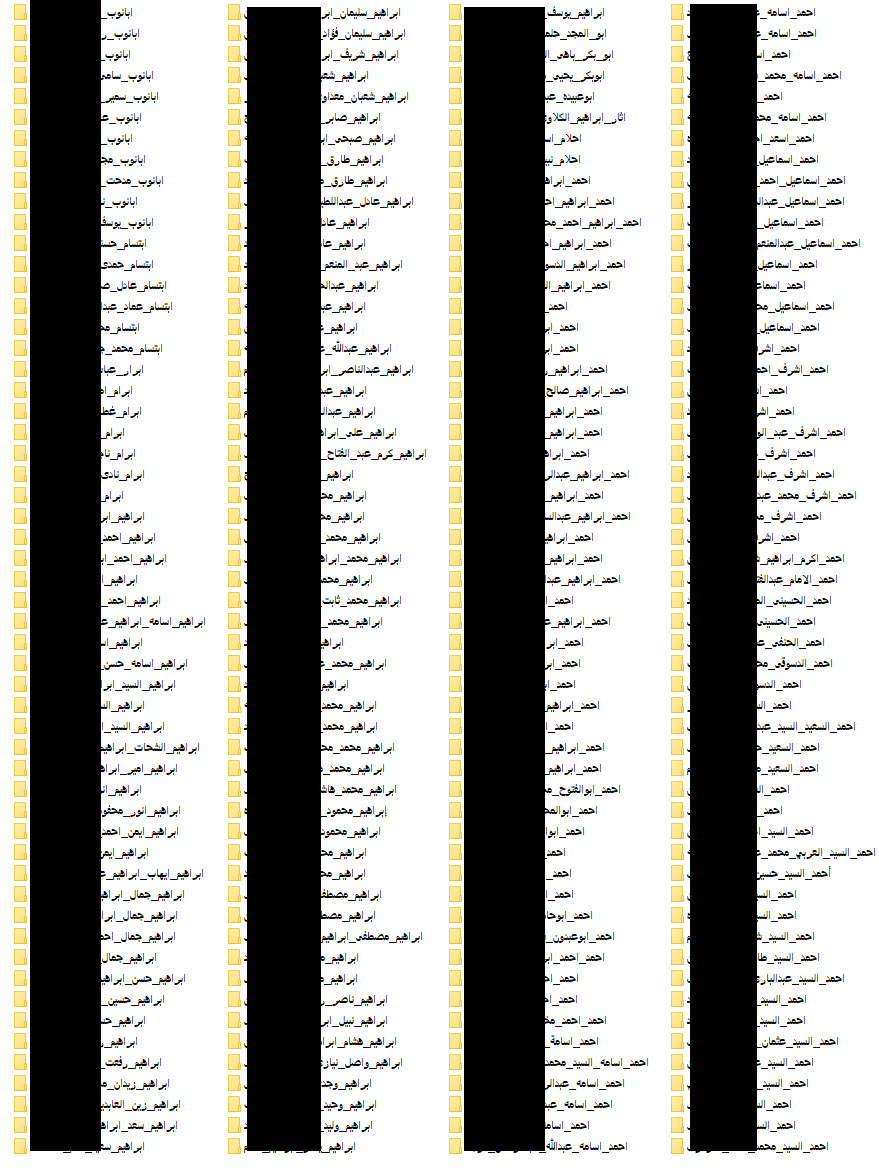
Figure 3. Directory containing stolen user profile photographs
Because the platform primarily serves licensed professionals such as engineers and healthcare workers, the exposed dataset could enable highly targeted fraud campaigns or identity-based attacks against members of these professional communities.
Potential Impact
Targeted Social Engineering and Financial Fraud
Members of professional syndicates typically belong to high-trust occupational groups, including engineers, physicians, and healthcare workers.
Access to accurate identity information may enable attackers to conduct highly targeted phishing or voice phishing campaigns, impersonating financial institutions, professional organizations, or government entities.
Financial Data Exposure
The platform functions as a fintech-enabled service, processing payments related to:
- annual membership subscriptions
- insurance services
- medical expenses
If payment-linked data or financial identifiers were accessed, affected users could face direct financial loss or fraudulent transactions.
Disruption of Medical and Welfare Services
The platform is integrated with systems used to manage medical benefits and hospital services for professional syndicate members.
Manipulation or disruption of these systems could lead to:
- incorrect medical records
- failure of appointment systems
- service disruptions affecting thousands of professionals
Such disruptions could have broader consequences for healthcare service availability and administrative operations.
Broader Targeting Activity
Additional attacker activity suggests attempted targeting of airline organizations across multiple regions, including:
- Middle East
- North Africa
- Europe
- Asia
However, no confirmed compromise logs were identified for these attempted attacks.
This pattern indicates that the observed infrastructure may have been used as part of a broader opportunistic intrusion campaign targeting organizations operating critical service platforms.
Conclusion
The compromise of a digital services platform serving Egypt's professional syndicate ecosystem highlights the risks posed when platforms aggregating identity, financial, and healthcare-related information are targeted by attackers.
The confirmed exfiltration of approximately 9,000 records may enable highly targeted fraud campaigns, particularly when the affected individuals belong to trusted professional communities.
Organizations operating centralized digital platforms for professional or government-linked communities should prioritize strict data protection controls, continuous infrastructure monitoring, and rapid incident response capabilities to mitigate the risk of exploitation and downstream abuse.