Active SQL Injection Campaign Targeting Global Payment and Enterprise Services
By Threat Intelligence Unit
Overview
Oasis Security identified an active SQL injection campaign operated through attacker infrastructure located in Canada.
The campaign targeted 35 websites, with confirmed successful SQL injection exploitation and data exfiltration affecting three organizations operating in the payment, real estate, and developer service sectors.
Attacker-side artifacts indicate coordinated and deliberate exploitation rather than opportunistic scanning.
Campaign Summary
Adversary Infrastructure
- IP:
72.11.148.141 - Country: Canada
Target Scope
- Total targets: 35 websites
- Confirmed compromises: 3 websites
- Attack Vector: SQL Injection
The attacker infrastructure appears to have been used to manage exploitation attempts and collect extracted database contents.
Confirmed Compromised Targets
1. Global Payment Processing Platform
- Domain: pay********.com
- Sector: Global Payment Services
A global payment service provider supporting credit card and localized payment processing across approximately 200 countries and regions.
SQL injection exploitation was identified against a payment-related service endpoint. As shown below, the attacker successfully enumerated the backend database structure — confirming a compromise of the underlying MySQL database.
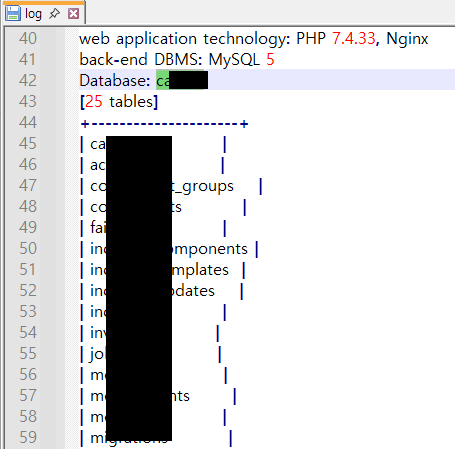
Figure 1. Enumerated database tables confirming successful SQL injection compromise on pay********.com
Further, the extracted subscribers.csv contains structured subscriber records, indicating successful SQL injection with database read capability.
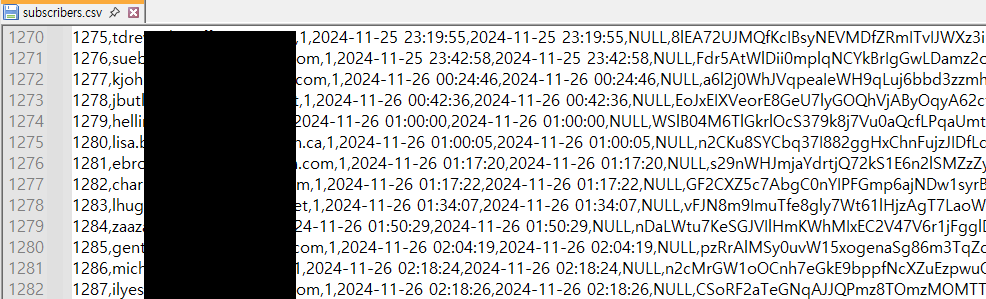
Figure 2. Sample records from the extracted subscribers.csv
2. Developer Demonstration Platform
- Domain: fast**************.com
- Sector: Developer Services
A developer-oriented domain used for tutorials, demonstrations, or technical experimentation leveraging FastSpring-related technologies.
SQL injection exploitation was identified against a service endpoint, resulting in unauthorized access to the backend database. The log file confirms successful enumeration of MySQL databases, including identification of the operational ios database. The listing of 61 internal tables demonstrates direct database-level access via SQL injection.
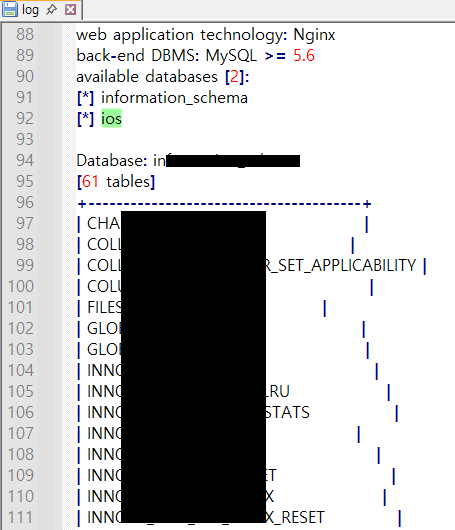
Figure 3. SQLMap log confirming successful enumeration of 61 tables from fast**************.com
3. Real Estate Services Platform
- Domain: hect********.com
- Sector: Real Estate / Asset Management
A corporate-focused real estate services platform offering asset management and property-related solutions.
The logs below confirm successful enumeration of the backend MySQL database, including identification of the database name and enumeration of 56 internal tables. The disclosure of DBMS version information and structured table listings indicates successful SQL injection enabling direct database-level access.
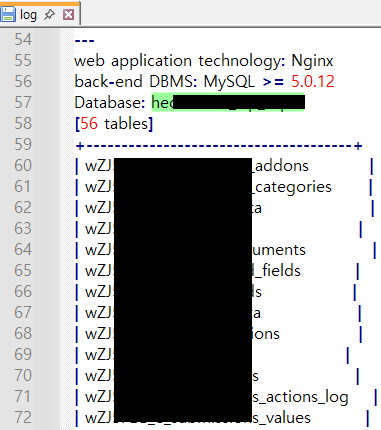
Figure 4. Enumerated database tables confirming successful SQL injection compromise on hect********.com
Risk Implications
SQL injection remains a critical, high-impact vulnerability when exposed in production environments. This campaign demonstrates that successful exploitation results in confirmed database enumeration and data exfiltration across enterprise-grade platforms.
Organizations operating externally accessible web applications should enforce strict parameterized query implementation, conduct continuous application-layer security testing, and monitor for anomalous database query patterns. Rapid remediation of input validation flaws is strongly advised, particularly for services handling sensitive user or financial data.
Conclusion
This campaign highlights the ongoing operational risk associated with unremediated SQL injection vulnerabilities across externally exposed enterprise systems. The confirmed compromise of payment-related and corporate service platforms — sectors handling sensitive financial and client data — suggests financially driven objectives, with potential for follow-on access monetization or resale of exfiltrated data.
The persistent risk posed by insufficient input validation and exposed database interfaces underscores the need for proactive defense. Continuous monitoring of attacker infrastructure and robust web application security controls remain critical to reducing exploitation-driven data breaches.