Identification of Public IP Address of Instant Money Shop, Bitcoin Mixer Sites
By Threat Intelligence Unit
Executive Summary
- A dark web marketplace offering Western Union Money Transfer Control Numbers (MTCNs) was identified.
- The same infrastructure was found hosting a cryptocurrency mixing service.
- Public-facing IP exposure suggests weak operational compartmentalization.
Site Analysis
The identified hidden service advertises access to Money Transfer Control Numbers (MTCNs) generated through Western Union transactions.
MTCNs function as transaction reference identifiers. In many transfer scenarios, knowledge of both the transaction code and recipient information may allow funds to be collected. For this reason, such identifiers must be treated as sensitive financial data.
Identified Onion Service
wucash2a6zntu6d3ib3qsfxo3gblhtj4f5yla4uvhmk35nejuzq4psyd.onion
The marketplace promotes discounted withdrawal access, including examples such as:
- $100 transfer listed at approximately $60
- $1,000 transfer listed at approximately $400
This pricing structure is consistent with monetization of compromised or fraudulently obtained financial transfer data.
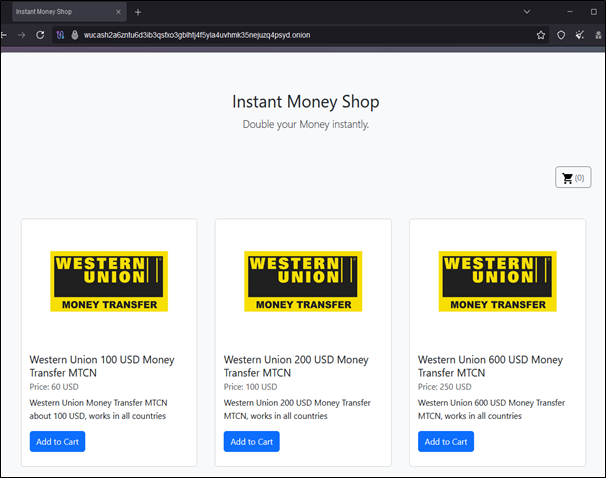
Figure 1. Instant Money Shop site
Infrastructure Analysis
Public IP Attribution
Through Oasis Security’s dark web infrastructure correlation platform Arthur, backend hosting infrastructure associated with the onion service was identified.
- Public IP Address:
170.75.***.*** - Country: Canada
The presence of a publicly routable IP indicates that the service backend is not fully isolated within Tor-only infrastructure.
Surface Web Exposure
Investigation of TCP Port 80 on the same IP address revealed a publicly accessible directory-style page referencing multiple hidden services, including the MTCN-related listing.
This configuration suggests:
- Shared hosting of multiple illicit services
- Incomplete separation between Tor-facing and public-facing components
- Elevated risk of infrastructure fingerprinting
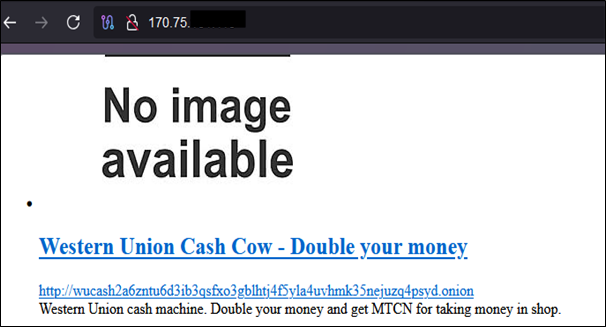
Figure 2. Public-facing web service discovered on same IP
Co-Hosted Cryptocurrency Mixing Service
Further analysis identified an additional onion service operating from the same infrastructure:
tordir3ochyabj5s7qpebkfjg5bvp44vfepdprdiu3p73eocqrvcxqqd.onion
The service advertises Bitcoin transaction anonymization functionality.
Cryptocurrency mixing platforms are commonly leveraged to obscure fund origin and transaction trails, particularly in financially motivated cybercrime ecosystems.
The co-location of:
- Financial transfer credential resale
- Cryptocurrency laundering functionality
Indicates a broader financial abuse infrastructure rather than an isolated fraud service.

Figure 3. Co-hosted Bitcoin Mixer site
Conclusion
The identified dark web marketplace demonstrates how financial transaction identifiers can be commercialized within illicit ecosystems.
Infrastructure analysis revealed that:
- Backend hosting is linked to a publicly exposed IP
- Multiple illicit services are co-hosted on the same server
- Operational isolation appears incomplete
Organizations in the financial transfer sector should continuously monitor transaction identifier exposure patterns and assess potential misuse vectors.
Ongoing infrastructure monitoring is recommended to mitigate financial crime risk.