Global Indiscriminate SQL Injection Campaign Impacting Public, Educational, and Commercial Organizations
By Threat Intelligence Unit
Overview
Oasis Security identified a large-scale automated attack campaign involving SQL injection exploitation, systematic data exfiltration, and deployment of obfuscated PHP web shells for persistence.
The activity targeted a broad range of organizations across multiple countries, including government agencies, universities, and private companies in the Philippines, India, Argentina, Malawi, South Korea, and others.
Analysis indicates financially motivated, indiscriminate exploitation focused on maximizing the number of compromised systems rather than targeting a specific sector or geography.
Executive Summary
- Large-scale automated SQL injection activity leveraging sqlmap and web shells to compromise multiple web applications
- Widespread impact across government, educational, and commercial organizations in multiple countries
- Exposure of approximately 28 million browser-stored credentials, including records associated with government domains (
.gov) - Observed compromises and credential harvesting indicate elevated risk of follow-on intrusions and data monetization
Notably affected organizations include Philippine government research institutions, multiple universities, and Korean association websites.
Adversary Infrastructure Overview
Analyzed C2 Server Information
Approximately 10,000 server-side files were obtained from the attacker-controlled IP address:
- IP Address:
46.8.226.22 - Location: Hong Kong
This C2 server functioned as a centralized aggregation point for attack tooling, SQL injection outputs, web shell artifacts, and exfiltrated data.
SQL Injection–Driven Exfiltration Activity
The attacker relied heavily on sqlmap to automate SQL injection exploitation across dozens of vulnerable websites.
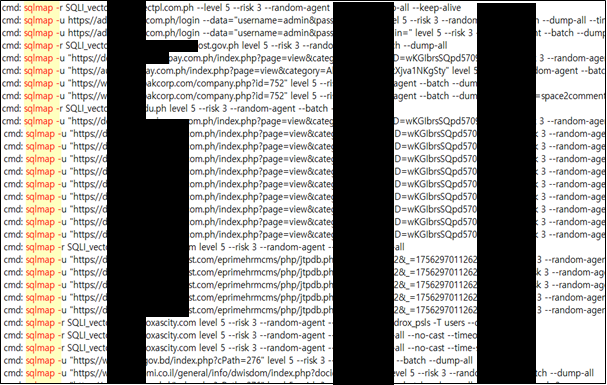
Figure 1. sqlmap command history demonstrating automated SQL injection exploitation across multiple target websites
A total of 58 domain-named folders were identified within sqlmap output directories, indicating successful exploitation attempts.
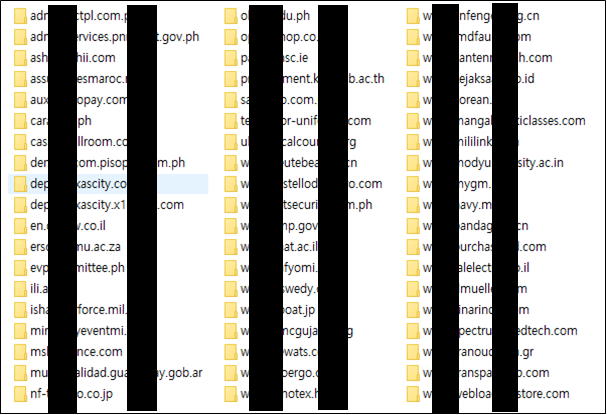
Figure 2. sqlmap result directories illustrating large-scale automated SQL injection activity
Confirmed SQL injection victims include multiple organizations across government, education, and commercial sectors, including:
- A government-affiliated research institute supporting critical energy infrastructure in the Philippines
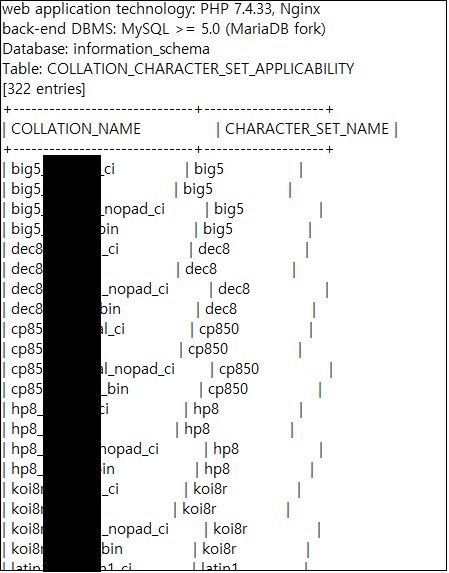
Figure 3. Extracted sqlmap artifacts demonstrating successful SQL injection–based database access
- A municipal education department in the Philippines

Figure 4. Extracted sqlmap artifacts showing successful SQL injection–based table dumping
- An insurance industry association in the Philippines
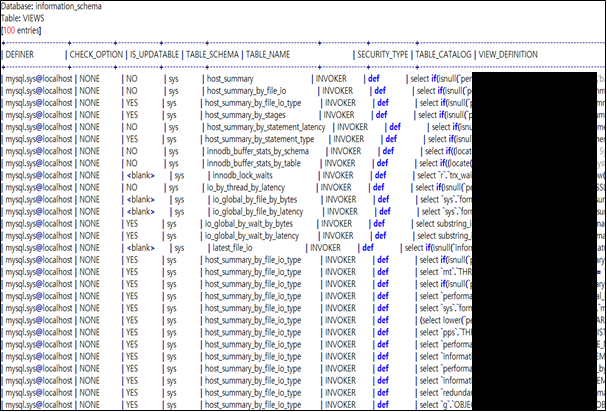
Figure 5. sqlmap output showing successful database metadata enumeration via SQL injection
- An RFID technology vendor
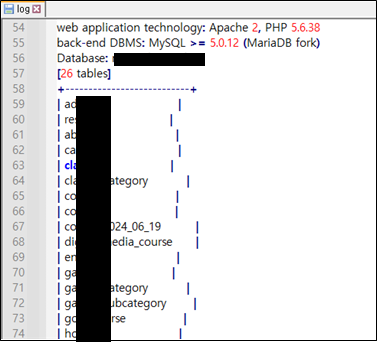
Figure 6. sqlmap output showing successful SQL injection exploitation
This confirms broad targeting of public-sector, educational, and commercial entities.
Exfiltrated Data Artifacts
Numerous SQL dumps and extracted files were identified within attacker directories, including:
- A vocational training and skills development organization in South Korea (
db_2025-10-02-0706.sql) - A child welfare–related government agency in the Philippines
- A science and technology program monitoring system operated by the Philippine government
- A public university campus network in the Philippines
- A healthcare research information management system operated by a public university in Malawi
- A municipal government web platform in Argentina
- A regional university email service platform in the Philippines
- Web hosting management panels
- Manufacturing and RF technology vendors across Italy, Hong Kong, and other regions
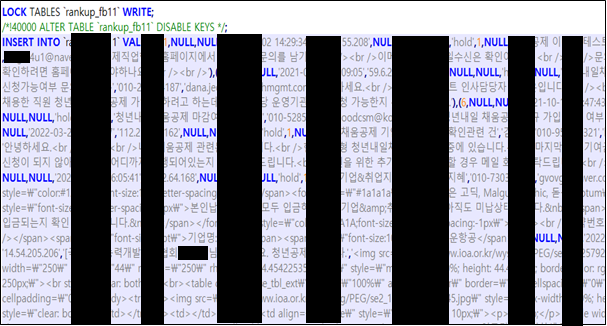
Figure 7. Extracted SQL artifacts indicating successful table access from a vocational training and skills development organization in South Korea
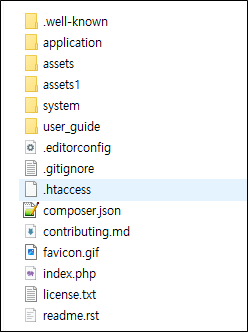
Figure 8. Extracted file system artifacts on a server operated by a child welfare–related government agency in the Philippines
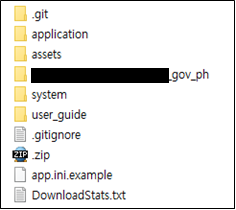
Figure 9. Extracted artifacts on a science and technology program monitoring system operated by the Philippine government
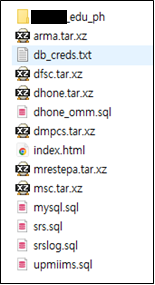
Figure 10. Extracted artifacts on a university in the Philippines
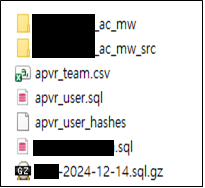
Figure 11. Extracted artifacts on a healthcare research information management system operated by a public university in Malawi
The diversity of victims reinforces the assessment of opportunistic mass exploitation rather than targeted espionage.
Web Shell Deployment and Persistence
The attacker deployed four obfuscated PHP web shells (Buset.php, anbu.php, b0y-101.php, and gecko.php) to maintain access to compromised systems.
One identified shell (Buset.php) used the password:
tidaksemudahituferguso
This phrase corresponds to Indonesian slang meaning “It’s not that easy, Ferguso.”
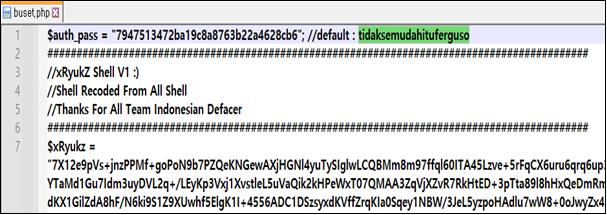
Figure 12. Extracted snippet from a web shell (Buset.php)
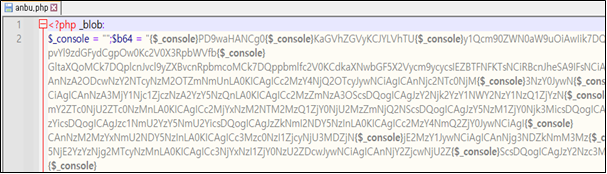
Figure 13. Extracted snippet from a web shell (anbu.php)
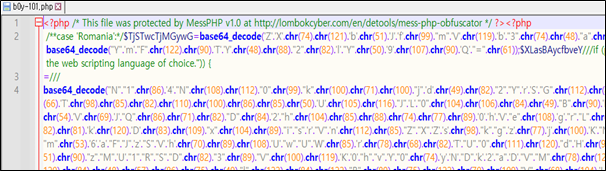
Figure 14. Extracted snippet from a web shell (b0y-101.php)
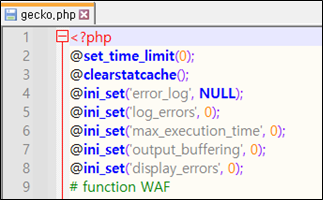
Figure 15. Extracted snippet from a web shell (gecko.php)
A webshells file contained four web shell paths. At the time of investigation, two of these paths were confirmed to be active.
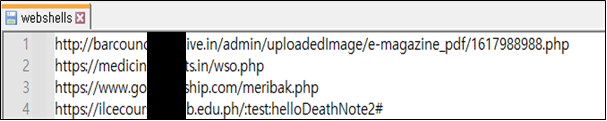
Figure 16. A list of four web shell paths in a webshells file
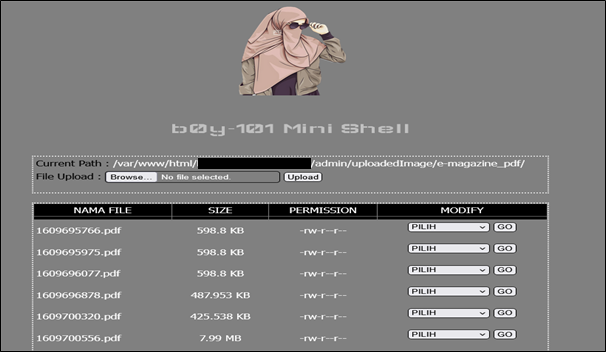
Figure 17. Active web shell interface observed via a web shell path
Additionally, 26 web shell paths were identified in the shells file, several of which were confirmed to be active at the time of investigation.
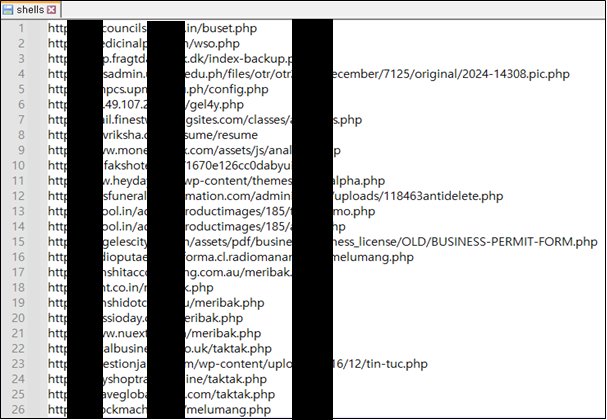
Figure 18. A list of 26 web shell paths in a shells file
Credential Exposure and Follow-On Risk
A file labeled ulp.txt contained approximately 28 million browser-stored auto-login credential records.
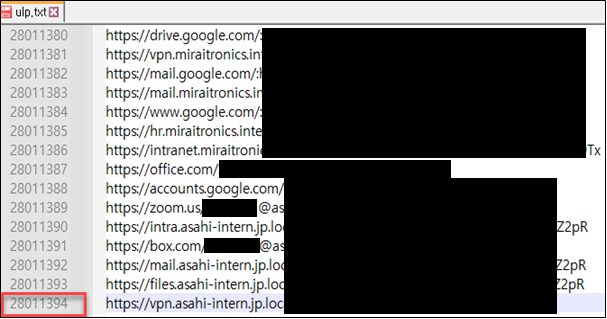
Figure 19. Excerpt from ulp.txt showing browser-stored auto-login credential records
Among these:
- Approximately 680,000 entries contained
.govdomains
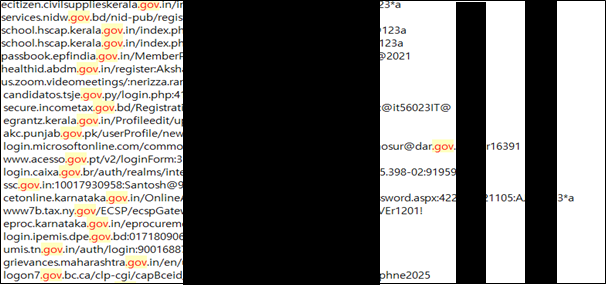
Figure 20. Government-domain credential artifacts extracted from ulp.txt
- Approximately 4,700 entries were associated with South Korean government (
go.kr) domains
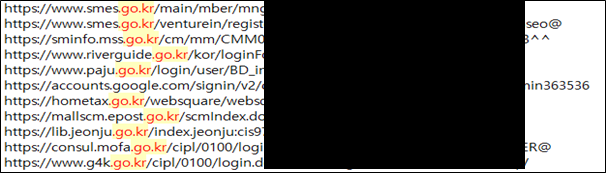
Figure 21. South Korean government credential artifacts extracted from ulp.txt
This represents a significant risk for credential reuse–based intrusion campaigns.
Using these credentials, the attacker is assessed to have obtained remote access to at least eight additional organizations, including:
- Funeral and cremation services (United States)
- Wedding venue platforms (United States)
- Hosting control panels
- VPS hosting providers
- Multiple Philippine university systems
- Asset monitoring services in the UAE
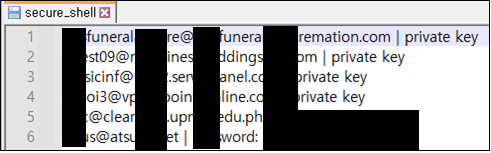
Figure 22. Extracted credential artifacts showing six confirmed remote access entries in secure_shell
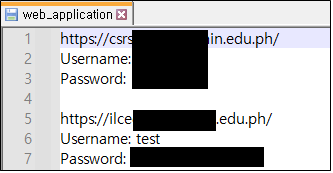
Figure 23. Extracted credential artifacts showing two confirmed remote access entries in web_application
These accesses represent confirmed compromises and are assessed to have provided operational footholds for further exploitation.
Assessment
Observed artifacts suggest a repeatable operational pattern involving automated SQL injection exploitation, data exfiltration, deployment of PHP web shells, aggregation of stolen credentials, and direct system compromise using harvested login data.
Victim selection appears indiscriminate, consistent with profit-driven cybercrime.
The presence of a massive credential dataset strongly suggests intent to:
- Conduct further lateral intrusions
- Resell access on underground marketplaces
- Enable ransomware or secondary compromise campaigns
Conclusion
This operation highlights the continued effectiveness of basic exploitation techniques—such as SQL injection and web shells—when combined with automation and large-scale credential harvesting. The exposure of approximately 28 million credentials materially increases downstream risk across multiple regions and sectors.
To reduce exposure, organizations should prioritize regular vulnerability scanning and timely patch management, deploy web application firewalls, monitor for unauthorized web shell artifacts, enforce strong credential hygiene with multi-factor authentication, and proactively detect anomalous database access patterns.
Without these baseline controls, opportunistic attackers can rapidly escalate minor web application weaknesses into widespread compromise and follow-on intrusion activity.