Multiple Active Exploitation Campaigns: Oracle EBS RCE, React2Shell RCE, and Large-Scale WordPress Credential Harvesting
By Threat Intelligence Unit
Overview
This post presents analysis of three distinct attacker operations identified through exposed command-and-control (C2) infrastructure and attacker-side artifacts.
The observed activities include Oracle E-Business Suite exploitation via CVE-2025-61882 resulting in oracle service account–level compromise, web application RCE via CVE-2025-55182 with verified OS-level command execution, and large-scale WordPress credential harvesting affecting over 1,300 websites.
Each campaign demonstrates active exploitation with attacker-side validation, highlighting deliberate post-compromise activity rather than opportunistic scanning.
Oracle EBS CVE-2025-61882 Exploitation with Oracle User-Level RCE
Key Findings
- Active C2 infrastructure was discovered during exploitation of Oracle EBS CVE-2025-61882.
- Confirmed exploitation of Oracle E-Business Suite via CVE-2025-61882 resulted in oracle service account–level remote code execution on multiple hosts.
- Attacker logs reference approximately 1000 application-level compromised IP addresses, including systems located in the United States (7) and Norway (1).
Adversary Infrastructure
- C2 IP:
162.248.227.54 - Country: US
The C2 server hosted attacker artifacts demonstrating successful execution within Oracle application contexts, including repeated privilege validation outputs.
Oracle EBS CVE-2025-61882
- A critical vulnerability in Oracle E-Business Suite that allows unauthenticated remote attackers to execute arbitrary code within application components.
- The flaw affects externally exposed Oracle EBS environments and can be exploited without prior authentication.
In this campaign, attacker-controlled artifacts confirm successful exploitation of CVE-2025-61882 resulting in oracle service account–level remote code execution across multiple Oracle EBS hosts.
Exploitation Validation Artifact
- According to annotations embedded in the log, this operation leveraged Oracle EBS CVE-2025-61882.
- 1,037 IP addresses are referenced in the exploitation results, representing Oracle EBS hosts where execution validation was attempted.
- Among these, systems located in the United States (7) and Norway (1) were explicitly observed.
- The
uid=oracleexecution context displayed across entries confirmed application-level compromise.
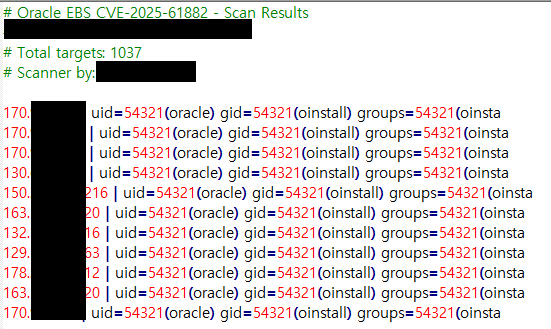
Figure 1. Oracle EBS exploitation validation logs
Remote Code Execution via CVE-2025-55182 exploitation
Key Findings
- A C2 server was discovered hosting attacker-side artifacts associated with exploitation of CVE-2025-55182.
- The attacker successfully compromised approximately 42 target websites, with confirmed post-exploitation activity.
- Command execution was validated through execution of OS-level commands.
Adversary Infrastructure
- C2 IP:
195.178.110.73 - Country: Netherlands
The identified IP address appears to function as attacker-controlled infrastructure, hosting operational logs related to successful exploitation attempts.
React2Shell CVE-2025-55182
- CVE-2025-55182 is a remote code execution vulnerability in React2Shell deployments that allows unauthenticated attackers to execute arbitrary OS-level commands due to improper input handling.
- Successful exploitation provides direct system-level access, enabling follow-on activity such as full host compromise.
Attacker-Side Artifact
Attacker-side logs stored in vulnerable_targets.txt document confirmed exploitation results for approximately 42 targets.
Each entry includes command execution output from the compromised hosts, including results of the OS-level commands (e.g., id command).

Figure 2. Attacker-side log showing successful RCE validation via id command execution on compromised hosts.
This artifact functions as an exploitation verification log rather than a simple target list, indicating that the attacker actively validated remote code execution on each host.
Large-Scale WordPress Credential Harvesting
Key Findings
- Attacker-side artifacts were identified including a file containing suspected WordPress access credentials.
- The collected dataset contains WordPress login URLs paired with usernames and passwords, associated with 1,316 websites, indicating systematic credential harvesting and centralized aggregation.
Adversary Infrastructure
- C2 IP:
45.156.25.5 - Country: Netherlands
Attacker-Side Artifact
A text file, wp login 3.12.2025.txt, was identified containing suspected WordPress access credentials. The file contains 1,316 credential-formatted entries.
Each entry combines:
- The WordPress login endpoint (
wp-login.php) - A corresponding username
- A corresponding password
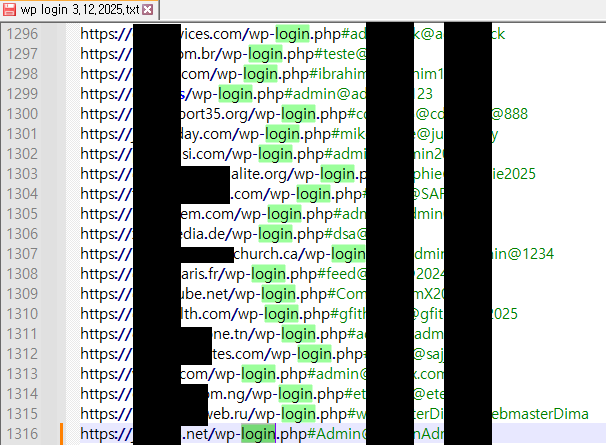
Figure 3. Credential-formatted entries in wp login 3.12.2025.txt
The data appears to function as an operational list for managing access to a large number of sites.
Conclusion
This post documents three independent intrusion activities in which threat actors leveraged known vulnerabilities and credential harvesting to gain application- and system-level access across diverse targets. Each case is supported by attacker-side artifacts confirming successful compromise and structured post-exploitation validation.
Taken together, these incidents highlight the ongoing risk posed by unpatched enterprise applications, exposed web services, and weak credential hygiene. Continuous infrastructure monitoring, timely remediation, and proactive credential protection remain essential to reducing exposure to exploitation-driven intrusions.