Backend Exposure of Dwebstore Financial Marketplace and Ganymede Drug Market
By Threat Intelligence Unit
Executive Summary
- Oasis Security identified a publicly exposed backend server supporting multiple dark web services, including a financial data marketplace (Dwebstore) and a drug marketplace (Ganymede).
- The services were traced to a shared public IP address, indicating backend infrastructure reuse across distinct illicit operations.
- Dwebstore sells sensitive financial information, including stolen financial credentials and transaction logs, along with fraud tools and tutorials.
- Ganymede operates on a different port of the same IP address and offers a wide range of narcotics, including prescription pills and controlled substances.
Site Analysis
Dwebstore operates as a dark web marketplace specializing in financially sensitive data, including:
- CashApp logs
- PayPal account information
- Visa and Mastercard data
- Bank logs
Four onion services associated with Dwebstore were identified, indicating a redundant deployment strategy designed to preserve availability in case of takedown or disruption.
Identified Onion Domains
- Primary Domain:
dwebc5kntr3tmndibeyl2yqr5edgws2tmjshkkh3ibs5vulmu7ylnbid.onion
- Mirror Domain:
dweb5sm34uzajabrjtl2jvznaaeop526p3sqi73hw4gur5ggkadqa3ad.onion
- Backup Domain 1:
ajwccz5y5jn33bwt2jiibcytg2pk4gdluwmij5i4qse3oahykq4fj7id.onion
- Backup Domain 2:
iqualowxvgqaijkrxy2xrl4peewievvvocenmt2qfbkxcto6cqt2anyd.onion
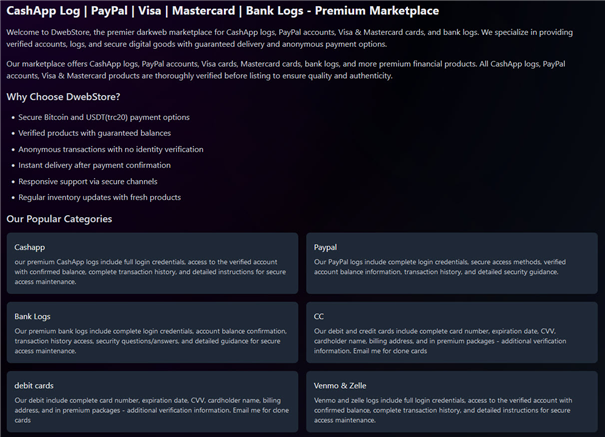
Figure 1. The homepage of the Dwebstore onion service
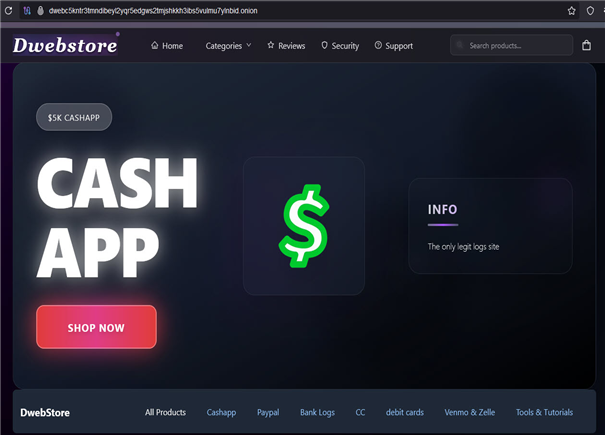
Figure 2. CashApp menu of the Dwebstore onion service
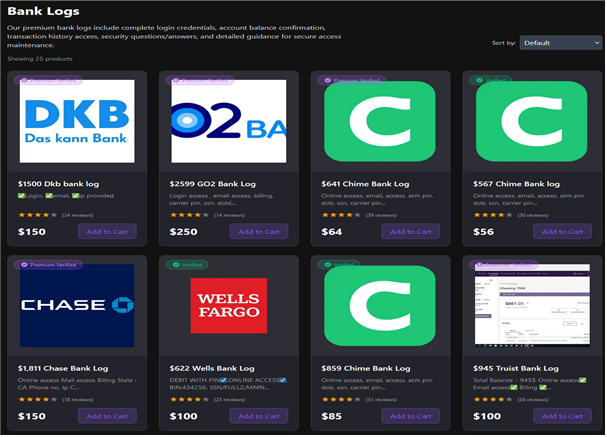
Figure 3. Bank Logs menu of the Dwebstore onion service
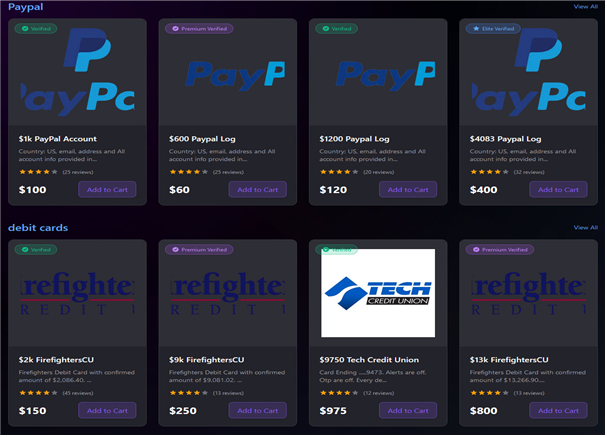
Figure 4. PayPal menu of the Dwebstore onion service
In addition to stolen financial records, the platform also provides fraud-related tools and tutorials, effectively lowering the technical barrier for cyber-enabled financial crime.
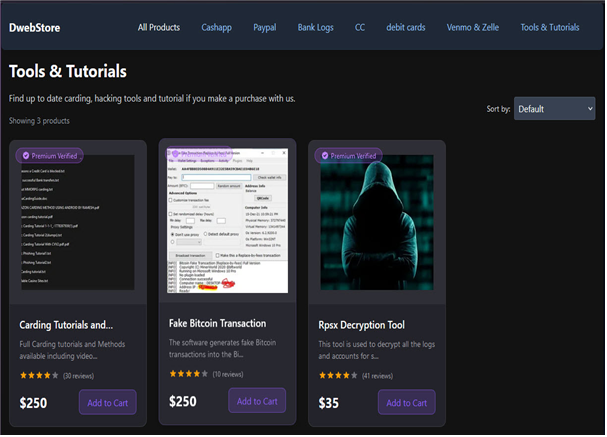
Figure 5. Tools & Tutorials menu of the Dwebstore onion service
Infrastructure Analysis and Public IP Discovery
Public IP Exposure
Using Oasis Security’s dark web intelligence service Arthur, the mirror onion service, dweb5sm34uzajabrjtl2jvznaaeop526p3sqi73hw4gur5ggkadqa3ad.onion, was correlated with the following public IP address:
- Public IP Address:
37.60.***.*** - Country: Germany
- Hosting Provider: CONTABO
- ASN: AS51167
Direct access to TCP port 8083 on this IP address revealed the same Dwebstore content observed via Tor, confirming that the hidden service backend was directly exposed to the public internet. This represents a clear operational security failure by the onion service operator.
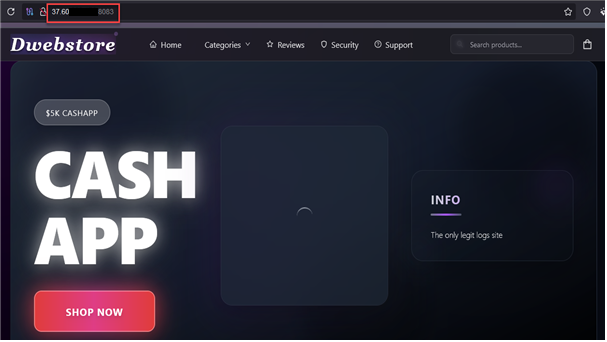
Figure 6. Dwebstore content observed via direct access to the public IP, 37.60.***.***
Co-located Drug Marketplace
Further analysis showed that the same IP address hosts an additional dark web marketplace, Ganymede, on a different port:
- Drug Market Port: 8060
- Admin Login Port: 8080
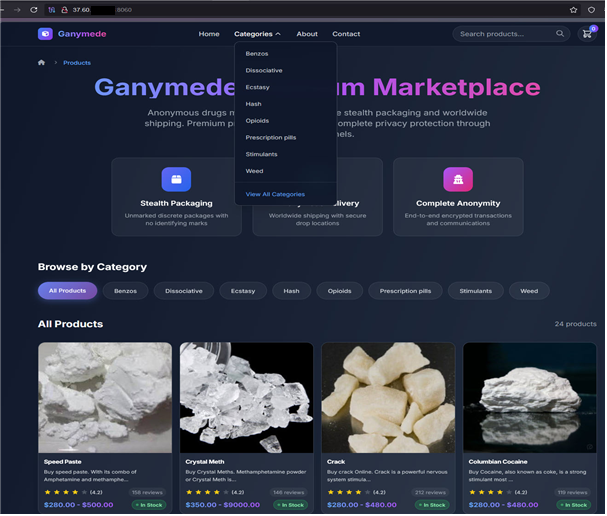
Figure 7. Ganymede service identified on port 8060 of the public IP, 37.60.***.***
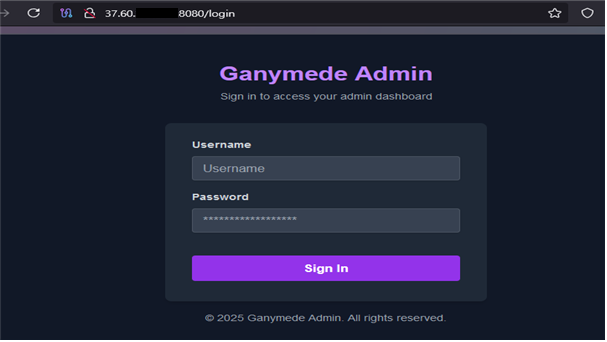
Figure 8. Ganymede admin login page accessed on port 8080 of the public IP, 37.60.***.***
This site was identified as the Ganymede onion service.
- Domain:
ganymyi2r6tc2hlnwaootgzwkibbp4nx35c2ivt3noiica22ssfazpqd.onion
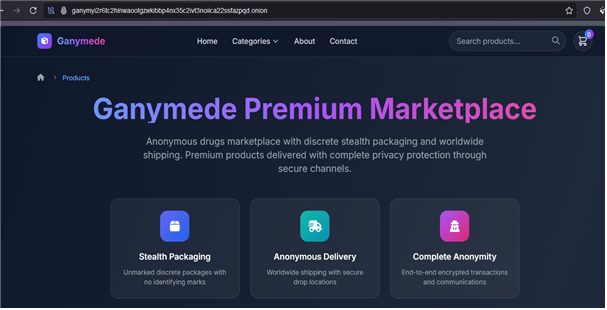
Figure 9. The Ganymede onion service
Ganymede offers a range of narcotics, including Benzodiazepines, Ecstasy, Opioids, prescription pills, stimulants, and cannabis products.
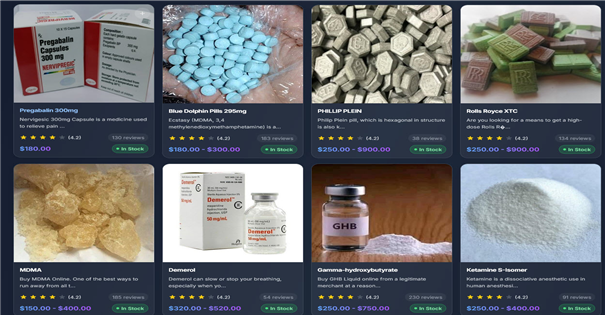
Figure 10. Product listings observed on the Ganymede onion service
The coexistence of a financial fraud marketplace and a drug trafficking platform on the same backend server strongly suggests infrastructure reuse by a single operator or closely affiliated actors, effectively forming a multi-crime backend hub.
At the time of analysis, the IP address showed no detections on VirusTotal, suggesting limited prior reporting rather than benign behavior.
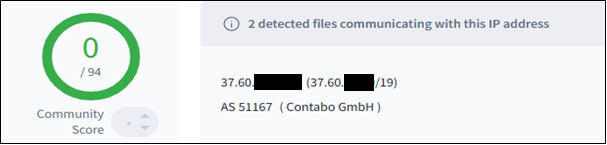
Figure 11. VirusTotal results showing no detections of 37.60.***.***
Conclusion
This investigation reveals a significant backend exposure linking Dwebstore, a financial data marketplace, and Ganymede, a drug trafficking platform, through a shared public IP address. The discovery underscores how backend infrastructure reuse across multiple illicit services creates observable linkages and increases attribution potential.
The concurrent operation of multiple criminal services on a single server materially increases attribution potential and presents a high-value opportunity for coordinated disruption. Continuous monitoring of this infrastructure, combined with engagement with hosting providers and relevant authorities, is recommended to mitigate ongoing financial fraud and narcotics distribution activities.