Internal Network Compromise and Automated Data Exfiltration Targeting Websites Referencing Vietnam Post Operations
By Threat Intelligence Unit
Overview
Oasis Security identified a targeted intrusion operation affecting multiple websites referencing Vietnam Post operations. The activity involved attacker-controlled infrastructure and post-compromise operations, including credential abuse, automated login workflows, and systematic data exfiltration.
Collected artifacts demonstrate deliberate, tool-assisted operations rather than opportunistic or one-off access, indicating a structured intrusion workflow focused on validating credentials, maintaining access, and extracting targeted data.
Executive Summary
- Targeted intrusion affecting multiple websites referencing Vietnam Post operations
- Use of the Vshell remote control tool for server access and persistence
- Custom Python tooling used for automated credential validation and data extraction
- Exfiltration of databases, credentials, and internal documents confirmed
- Linguistic and operational indicators suggest a Chinese-speaking attacker
Adversary Infrastructure Overview
Primary Attacker-Controlled Server
- IP Address:
154.216.177.215 - Country: Hong Kong
The Hong Kong–based server was identified as the primary attacker-controlled environment where multiple attack tools, operational logs, and exfiltrated files were stored and executed. Analysis indicates that this system functioned as the main operational node supporting command execution, credential automation, and data aggregation.
Attacker-Associated Access Node
- IP Address:
154.61.71.50 - Country: Netherlands
This IP address was identified through Vshell configuration artifacts (settings.conf). It is assessed to represent an attacker-side access point or intermediate node used to connect to the primary operational server, rather than a compromised victim system.
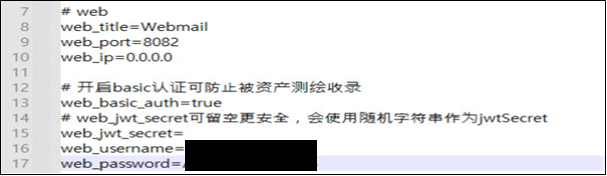
Figure 1. Excerpt from a Vshell configuration file (settings.conf)
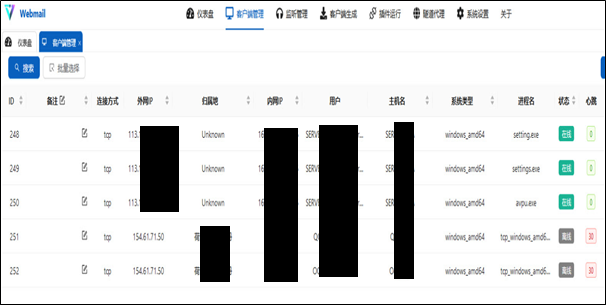
Figure 2. Vshell user interface showing an active connection associated with IP address 154.61.71.50
Compromised Systems Referencing Vietnam Post Operations
113.160.***.***(Vietnam)117.7.***.***(Vietnam)
These systems were confirmed as successfully accessed via Vshell connection logs (data.db) and are assessed to represent compromised internal systems associated with websites referencing Vietnam Post operations.
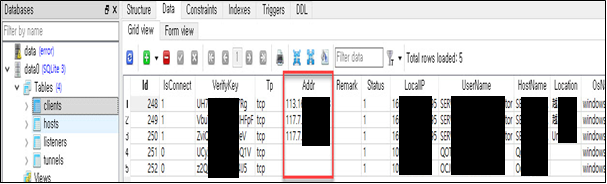
Figure 3. Vshell connection logs, data.db
Post-Compromise Tooling and Automation
Use of Vshell for Remote Control
The attacker leveraged the Vshell remote administration tool to maintain control over compromised systems. Connection records stored in data.db confirm successful access to multiple Vietnam-based hosts, while configuration files (settings.conf) reveal how the attacker authenticated to and interacted with the Vshell environment.
The presence of both configuration and operational artifacts indicates sustained access rather than a single-session compromise.
Custom Python-Based Attack Tooling
The analyzed Python scripts and related files were located within a directory labeled hb, which contained a mixture of Python scripts, text files, Excel spreadsheets, and image files. This directory appears to have functioned as a working folder used to store tooling, intermediate results, and outputs generated during the attack workflow.

Figure 4. Python scripts and related files in a directory hb
Analysis identified multiple custom Python scripts used to automate credential abuse and data collection:
dl.py
Implements logic designed to bypass CAPTCHA mechanisms during login attempts against websites referencing Vietnam Post operations.
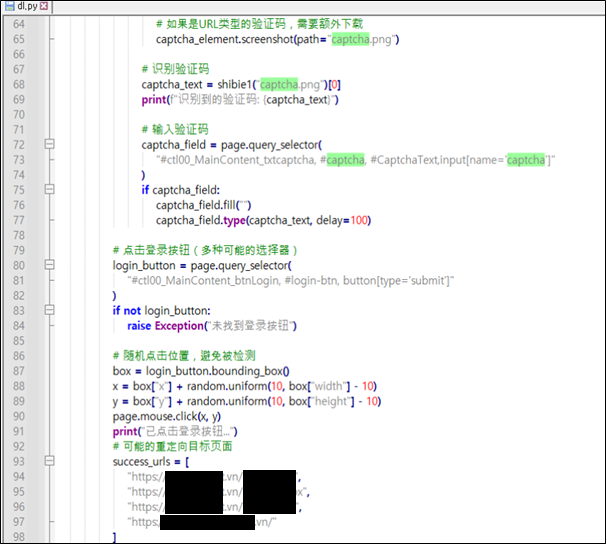
Figure 5. Excerpt from a Python script dl.py
dl2.py
Attempts authentication against a website believed to reference Vietnam Post operations using predefined username and password combinations.
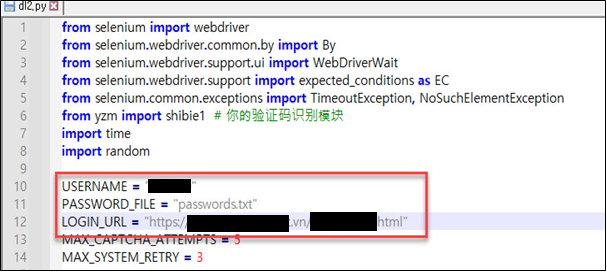
Figure 6. Excerpt from a Python script dl2.py
password.txt
Contains approximately 1,000 passwords used for automated login attempts.
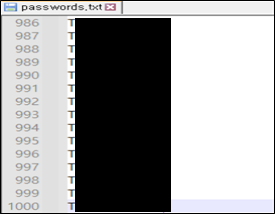
Figure 7. Excerpt from a text file password.txt
mm.txt
Stores validated login credentials, including domains, usernames, and passwords. Analysis indicates that approximately six accounts across two websites were successfully authenticated and verified.
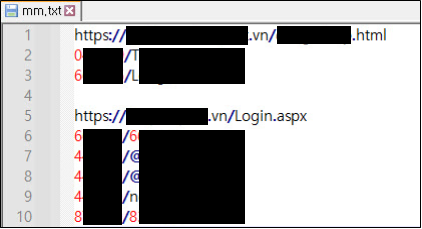
Figure 8. Excerpt from a text file mm.txt
post_bccptxt.py
Automates login using credentials stored inmm.txtand performs structured data extraction.
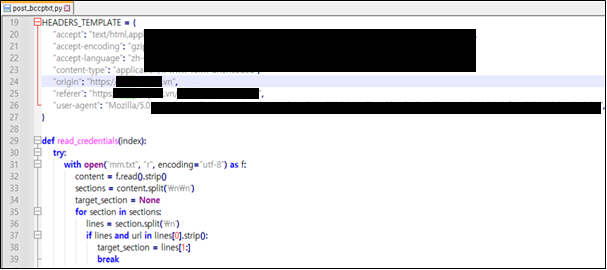
Figure 9. Excerpt from a Python script post_bccptxt.py
post_bcc_output3.xlsxandpost_output3.txt
Successfully exfiltrated data bypost_bccptxt.pyis written topost_bcc_output3.xlsxandpost_output3.txt
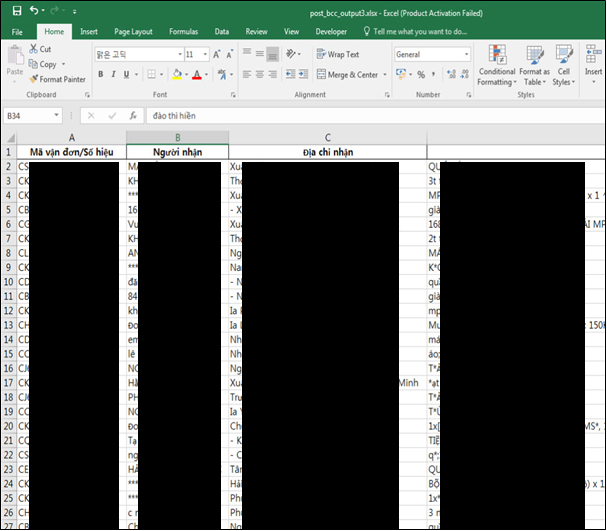
Figure 10. Excerpt from an Excel file post_bcc_output3.xlsx
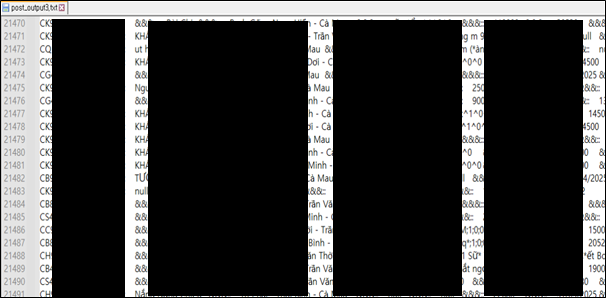
Figure 11. Excerpt from a text file post_output3.txt
In addition to these materials, a CSV file labeled 11.csv was identified within attacker-side directories. The file contained multiple subdomains referencing websites related to Vietnam Post operations. Based on available evidence, the file is assessed to represent an aggregated dataset collected or stored by the attacker.
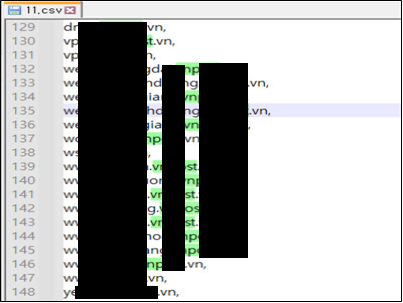
Figure 12. Excerpt from 11.csv
Data Exfiltration Evidence and Artifacts
Multiple artifacts confirm successful data exfiltration, including:
- Structured database files (
data.sqlite) - Internal documents (
1.pdf) - SQL dump files (
01.00.0000.sql)
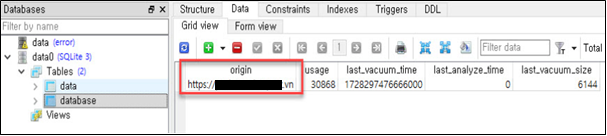
Figure 13. data.sqlite
Figure 14. Excerpt from 1.pdf
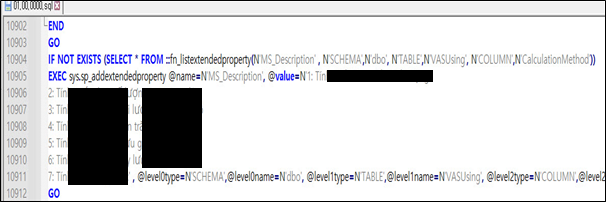
Figure 15. Excerpt from 01.00.0000.sql
Additional Post-Exploitation Activity
Further evidence of attacker activity was identified in additional tooling and logs:
- ffuf
Scan results stored inresults.jsonandffuf_results.jsonindicate directory and endpoint enumeration targeting websites referencing Vietnam Post operations.
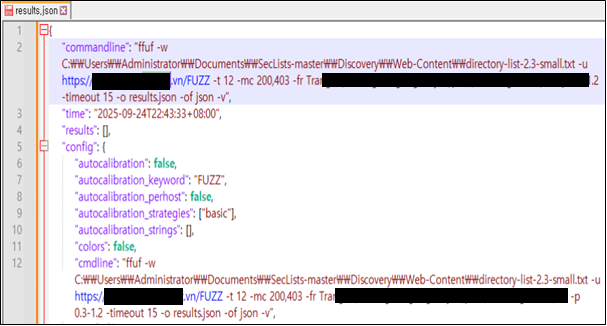
Figure 16. Excerpt from results.json
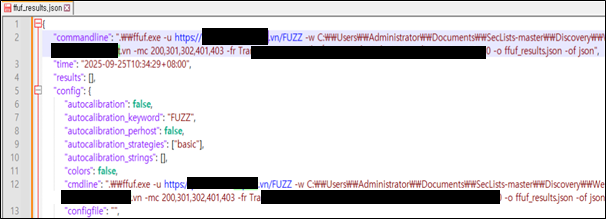
Figure 17. Excerpt from ffuf_results.json
- Metasploit
Command history files (history) indicate usage consistent with post-exploitation reconnaissance.
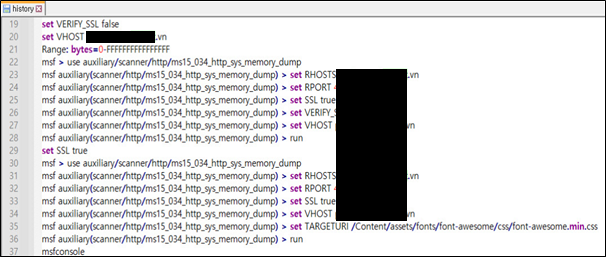
Figure 18. Excerpt from history
Threat Actor Indicators
Linguistic Indicators
Analysis of the Chrome browser history used by the attacker revealed repeated use of Google Translate to translate Vietnamese content into Chinese.
Multiple logs indicate Vietnamese text was translated into Chinese.
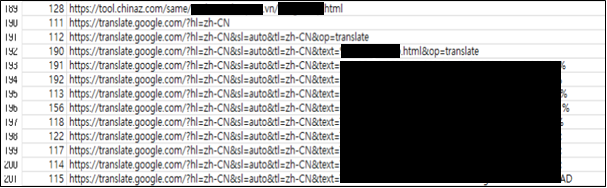
Figure 19. Repeated use of Google translate
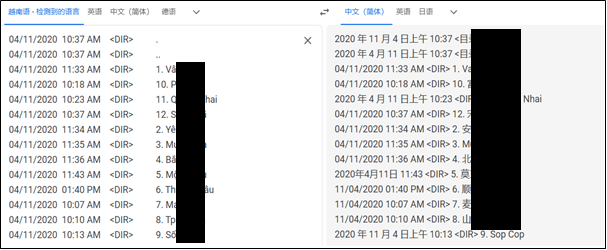
Figure 20. Langugae translation from Vietnamese to Chinese
Operational Indicators
- Use of the Hong Kong version of Google Search
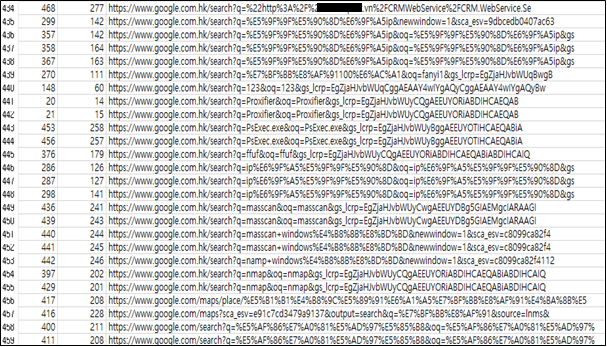
Figure 21. Use of the Hong Kong version of Google search
- Presence of a Proton Mail–based credential (
wang***@proton.me) inpasswords.txt
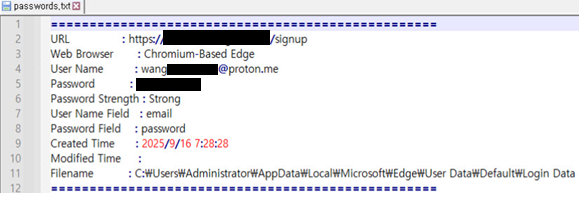
Figure 22. Attacker-attributed credential found in passwords.txt
While these indicators are insufficient for definitive attribution, they consistently suggest that the attacker is a Chinese-speaking individual or group rather than a native Vietnamese operator.
Conclusion and Recommendations
This intrusion highlights the elevated risk posed by attackers who successfully obtain internal network access. Once internal access is achieved, credential abuse and automation can enable rapid and repeatable data exfiltration with minimal additional exploitation.
To reduce exposure to post-compromise activities, organizations should maintain continuous visibility into internal assets and activity, enforce least-privilege access, and detect anomalous internal automation or data access.