Exploitation of Magento CVE-2025-54236: Independent Intrusions Leading to Root Compromise and Web Shell Deployment
By Threat Intelligence Unit
Overview
CVE-2025-54236 (SessionReaper) is a Magento vulnerability that enables attackers to bypass authentication by reusing improperly invalidated session tokens, potentially leading to full system compromise.
Oasis Security identified multiple independent intrusion incidents in which threat actors exploited CVE-2025-54236 against Magento environments across different regions. In one case, large-scale exploitation led to the compromise of 200+ websites worldwide and root-level access, while in another, the vulnerability was used to deploy web shells on Magento sites in Canada and Japan, enabling persistent access.
Mass Vulnerable API Discovery and Root Compromise via CVE-2025-54236 Campaign
Adversary Infrastructure
- C2 IP:
93.152.230.161 - Country: Finland
Key Findings
- Active C2 infrastructure was discovered orchestrating an ongoing campaign.
- An aggressive mass exploitation campaign was launched leveraging CVE-2025-54236.
- 1,000+ vulnerable Magento Commerce APIs were identified by the attackers.
- 200+ websites were fully compromised, with root access successfully obtained.
CVE-2025-54236 (SessionReaper)
- A Magento vulnerability that allows attackers to capture and replay reusable or improperly invalidated session tokens, enabling session hijacking and unauthorized account access.
- List of 1,460 APIs identified as vulnerable to CVE-2025-54236 exploitation, success_api_2025.txt
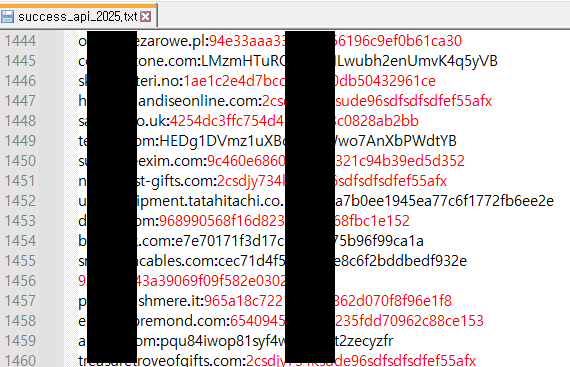
Figure 1. 1,460 vulneralbe APIs, success_api_2025.txt
Compromised Victims
- 216 sites were fully compromised via CVE-2025-54236 exploitation.
- 216 individual files of victim sites were identified as shown in Figure 2 where each file corresponds to a distinct compromised system.
- The files contain /etc/passwd-style user account listing, indicating full system compromise of the victim systems (Figures 3 and 4).

Figure 2. 216 victim sites identified
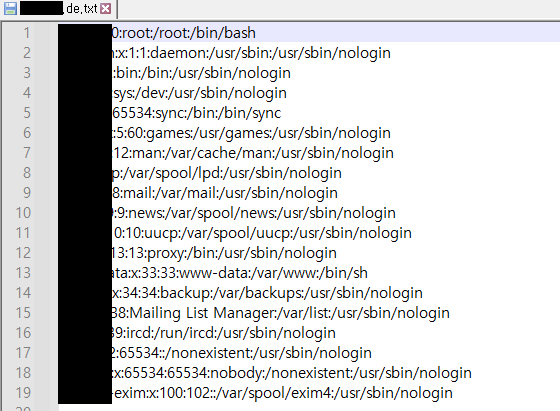
Figure 3. Excerpt from a leaked /etc/passwd file (1)
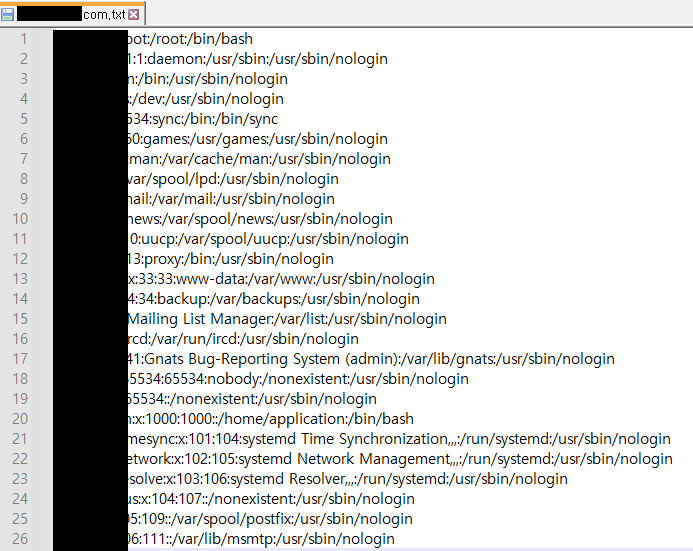
Figure 4. Excerpt from a leaked /etc/passwd file (2)
Canada and Japan Targeted: Webshell Attack via CVE-2025-54236 Exploitation
Adversary Infrastructure
- C2 IP:
115.42.60.163 - Country: HK
Key Findings
- Successful web shell upload attacks were conducted against Magento sites in Canada and Japan through exploitation of CVE-2025-54236.
- Uploaded web shells were deployed at attacker-controlled paths on victim servers, indicating full system compromise and persistent access.
Web Shell Deployment Evidence
- The logs confirm successful web shell uploads across multiple victim websites in Canada and Japan (Figures 5 and 6).
- The logs contain structured records identifying compromised sites, associated web shell access paths, and attacker-defined control parameters (Figures 7 and 8).
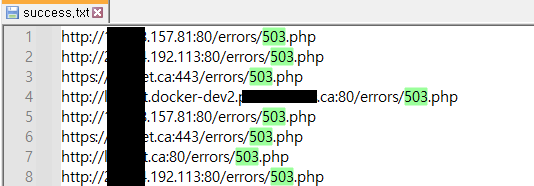
Figure 5. Logs Indicating Successful Web Shell Uploads
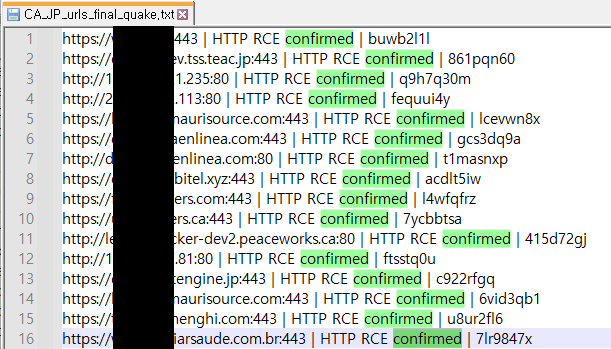
Figure 6. Successful Web Shell Uploads Targeting Sites in Japan and Canada
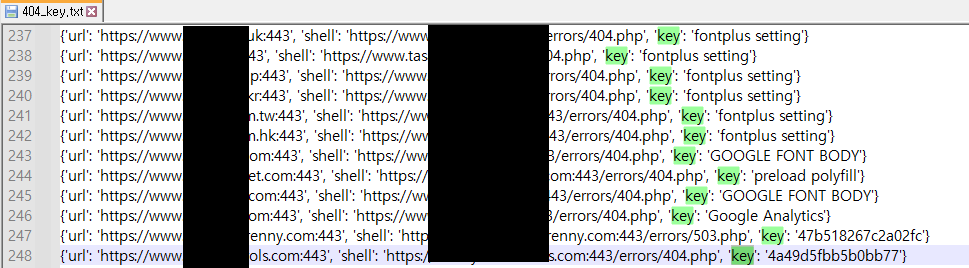
Figure 7. Structured log entries listing victim URLs, deployed web shell paths, and control keys, 404_key.txt
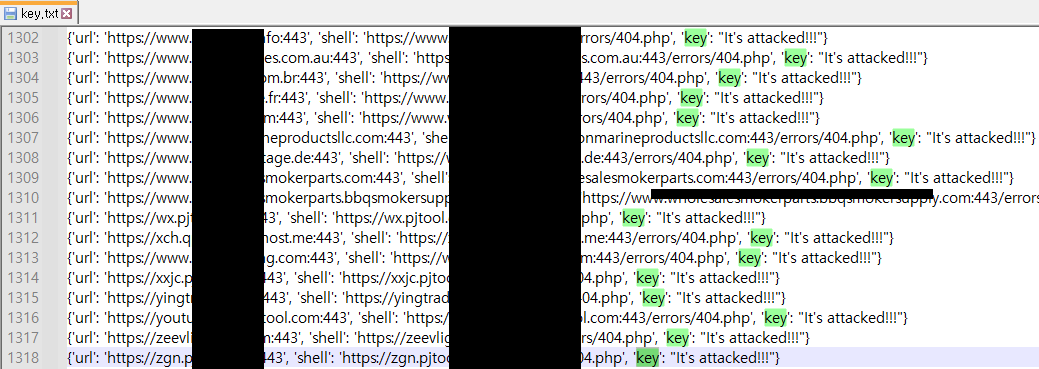
Figure 8. Structured log entries listing victim URLs, deployed web shell paths, and control keys, key.txt
Conclusion
This post documents multiple independent incidents in which different threat actors exploited CVE-2025-54236 (SessionReaper) against Magento environments. While the cases are not assessed to be part of a single coordinated campaign, all incidents demonstrate that the vulnerability is being actively abused for authentication bypass, full system compromise, and, in some cases, web shell deployment and persistent access.
Collectively, these incidents highlight the widespread and ongoing risk posed by unpatched Magento instances affected by CVE-2025-54236.