Identification of Public IP Address of Counterfeit Currency Sales Cash God
By Threat Intelligence Unit
Executive Summary
- A public IP address associated with the Counterfeit Currency Sales Cash God site was identifid.
- The same Cash God site was observed operating on an additional port on the same IP address.
Site Analysis
Cash God operates as a counterfeit currency marketplace accessible via the Tor network. The site advertises multiple denominations of forged banknotes and presents itself as an international supplier.
The service is accessible through two Tor hidden service (.onion) domains, indicating basic redundancy and availability considerations commonly observed among illicit marketplaces.
Identified Onion Domains
- Primary Domain:
cashgodwg3ksstzueceszgh2kizytgbim5xll7ssl32j5vgmshg3i2yd.onion
- Mirror Domain:
cashgodwx2x4kfcpfrvdj3uthok76yzo3angsow3drdpnjqvxndn3nqd.onion
The presence of a mirror domain suggests an attempt to maintain service continuity in the event of takedown or infrastructure disruption.
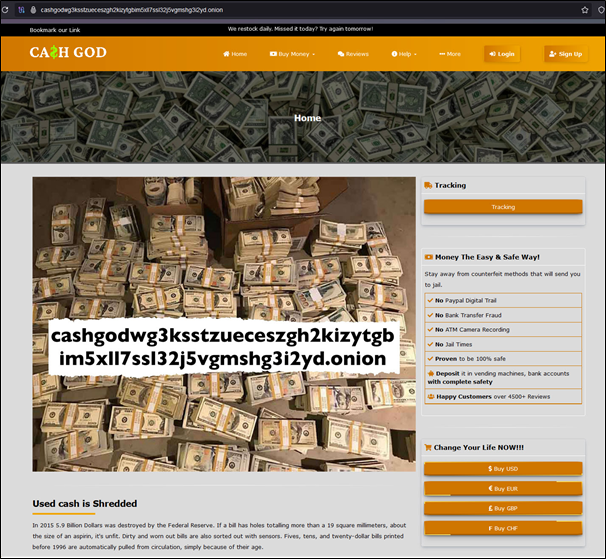
Figure 1. Cash God Site
Illicit Goods Offered
The following counterfeit banknote types were identified for sale on the platform:
- United States Dollar (USD)
- Euro (EUR)
- British Pound Sterling (GBP)
- Swiss Franc (CHF)
The diversity of supported currencies indicates a multi-regional targeting strategy rather than a single domestic focus.
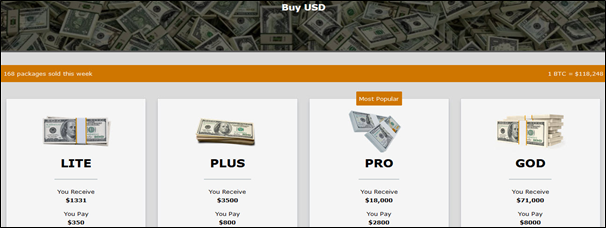
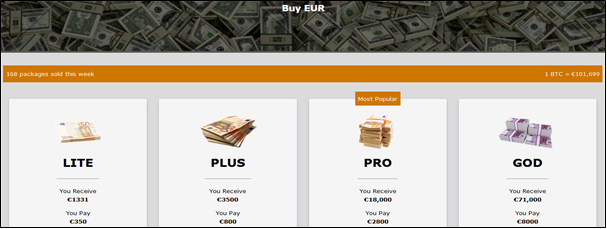
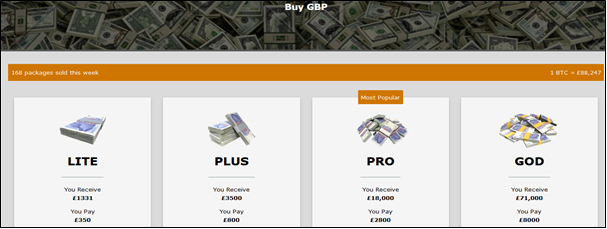
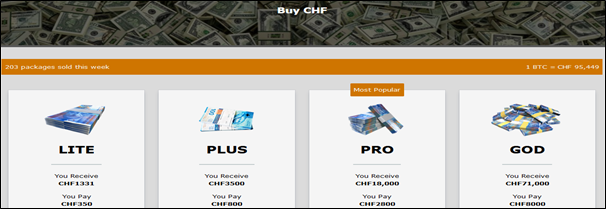
Figure 2. Counterfeit currencies for sale
Infrastructure Analysis and Public IP Discovery
Public IP Exposure
Using Oasis Security’s dark web infrastructure analysis service Arthur, the backend infrastructure supporting Cash God was identified.
- Public IP Address:
31.220.***.*** - Country: United States
- Hosting Provider: HOSTINGER
- ASN: AS47583
This confirms that the Tor hidden service is not fully isolated from the public internet.
Same Cash God Site accessible on the Clearnet
Insufficient segregation between Tor-facing and public-facing service components was identified.
- TCP Port 80 on
31.220.***.***serves identical web content to that observed on the Cash God Tor hidden service.
- Such configurations significantly weaken the anonymity guarantees typically sought by dark web operators and represent a recurring operational security failure in illicit service infrastructures.
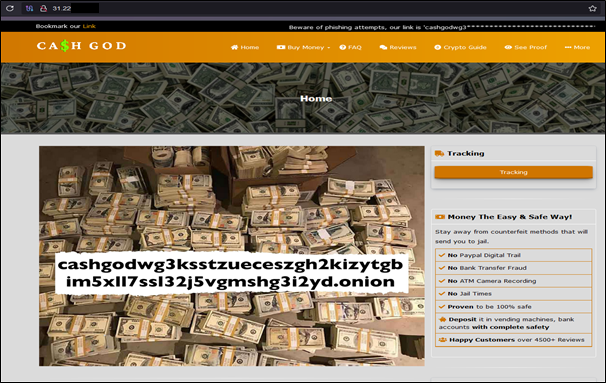
Figure 3. Cash God site accessible via clearnet
Conclusion
Cash God represents a dark web–hosted illicit service in which backend infrastructure exposure has reduced the effectiveness of its anonymity controls. Portions of the underlying backend infrastructure are directly accessible via a publicly routable IP address, indicating incomplete isolation between Tor-based and clearnet-facing components.
Continuous monitoring of this infrastructure is recommended to mitigate potential financial crime and fraud-related impacts.