AKIRA Ransomware Infrastructure Analysis: Dark Web Sites and Public IP Exposure
By Threat Intelligence Unit
Overview
The AKIRA ransomware group operates a structured extortion ecosystem leveraging Tor-based onion services for victim negotiation and public data disclosure. These services are supported by backend infrastructure that, while frequently rotated, exhibits consistent configuration characteristics.
Through dark web monitoring and infrastructure correlation performed via Arthur, Oasis Security’s proprietary dark web intelligence service, Oasis Security identified public-facing IP addresses associated with AKIRA’s data leak operations.
Executive Summary
- Active AKIRA ransomware campaigns observed across North America, Europe, and Australia.
- Over 250 organizations compromised since 2024, with significant impact on the manufacturing sector.
- Analysis identifies public IP exposure and recurring infrastructure reuse within AKIRA’s leak site operations.
AKIRA Dark Web Infrastructure
Negotiation Portal
- Onion Address:
akiralkzxzq2dsrzsrvbr2xgbbu2wgsmxryd4csgfameg52n7efvr2id.onion
This onion service functions as a negotiation portal, allowing ransomware victims to communicate with the attackers through a chat-based interface. Access is controlled via a unique victim identifier generated during the ransomware execution process.
Figure 1. AKIRA portal
Data Leak & Extortion Site
- Onion Address:
akiral2iz6a7qgd3ayp3l6yub7xx2uep76idk3u2kollpj5z3z636bad.onion
This site operates as AKIRA’s public data leak platform, disclosing victims whose data has already been published as well as pending victims whose data is scheduled for release if negotiations fail.
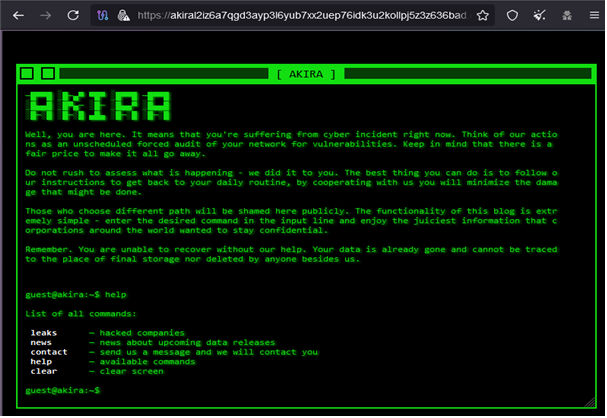
Figure 2. AKIRA's data leak and extortion site
Analysis of victim disclosures indicates that organizations based in the United States represent a significant portion of the affected entities. Posting activity also suggests increased operational activity by the group.
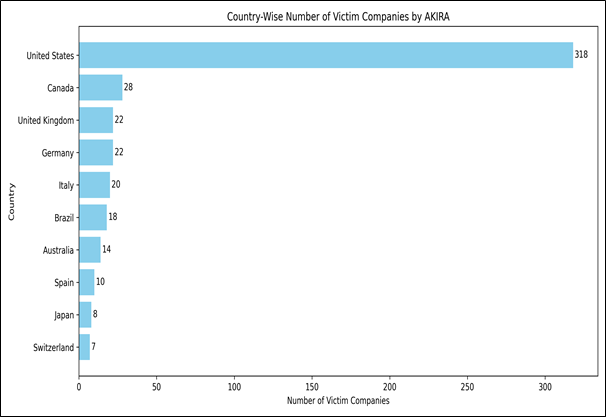
Figure 3. Country-wise victim companies
Infrastructure Analysis and Public IP Discovery
Identified Active Infrastructure
Through correlation of Tor service behavior and backend network exposure, the following public IP addresses were identified as supporting AKIRA’s leak site operations:
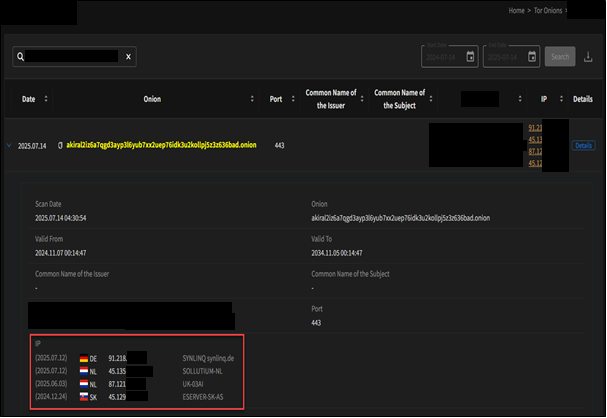
Figure 4. Identified AKIRA's infratructures by OASIS Security's Darkweb Intelligence service, Arthur
Active IP Addresses
| IP | Country | Provider | ASN |
|---|---|---|---|
91.218.***.*** | Germany | SYNLINQ | AS44486 |
45.135.***.*** | Netherlands | SOLLUTIUM | AS43641 |
Both IP addresses expose web services on TCP port 9443. Direct access to these services via the public IP addresses consistently returns HTTP 403 responses, including when accessed using Tor Browser, suggesting that the services may be intended to be accessed through Tor hidden service (.onion) endpoints rather than via direct IP-based access.
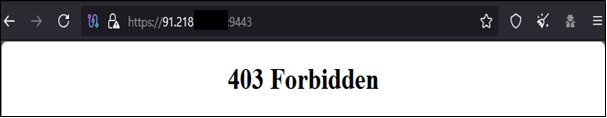
Figure 5. 403 Forbidden response from 91.218.***.***:9443 via direct access
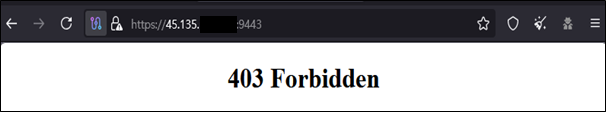
Figure 6. 403 Forbidden response from 45.135.***.***:9443 via direct access
Historical Infrastructure Correlation
Arthur also identified historical IP addresses previously associated with the same leak site infrastructure, demonstrating a consistent pattern of infrastructure rotation combined with configuration reuse.
Previously Observed IP Addresses
| Date | IP | Country | Provider | ASN |
|---|---|---|---|---|
| 2025-03-06 | 87.121.***.*** | Netherlands | 03AI | AS213725 |
| 2024-12-24 | 45.129.***.*** | Slovakia | ESERVER | AS61424 |
Despite changes in hosting providers and geographic locations, identical web service attributes were repeatedly reused across multiple infrastructure rotations.
Validation and Observations
VirusTotal confirms that all identified IP addresses correspond to legitimate.
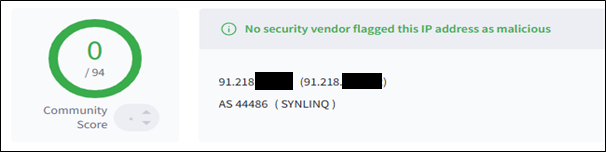
Figure 7. VirusTotal result showing no detections for 91.218.***.***
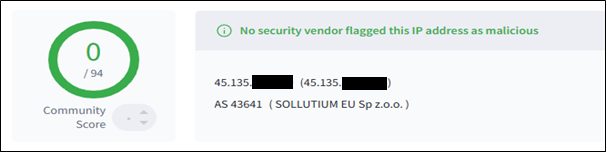
Figure 8. VirusTotal result showing no detections for 45.135.***.***
Conclusion
AKIRA ransomware continues to operate an active and evolving extortion infrastructure supported by Tor-based services and rotating public IP addresses. Although the group frequently changes hosting environments, repeated reuse of backend service configurations creates identifiable infrastructure patterns.
Continuous monitoring of dark web services and associated network infrastructure remains critical for early detection and proactive defense against ransomware operations.